Deploying Headscale on a VPS: Creating Your Own Private Mesh Network (VPN)
TL;DR
In this guide, we will deploy Headscale — an open-source implementation of the Tailscale control server — on a virtual private server (VPS) running Ubuntu 24.04/Debian 12. As a result, you will get your own mesh network where all your devices (laptops, servers, smartphones) are connected directly via WireGuard without third-party intermediaries. We will set up automatic TLS via Caddy, examine ACL configuration for security, and ensure system resilience with regular backups. This solution is ideal for those who value privacy and want full control over their network infrastructure in 2026.
- Technology: WireGuard + Headscale (Control Plane).
- Complexity: Medium (basic terminal skills required).
- Setup Time: 40-60 minutes.
- Result: A secure network with access to internal resources from anywhere in the world.
1. What we are setting up and why: The evolution of VPN in 2026
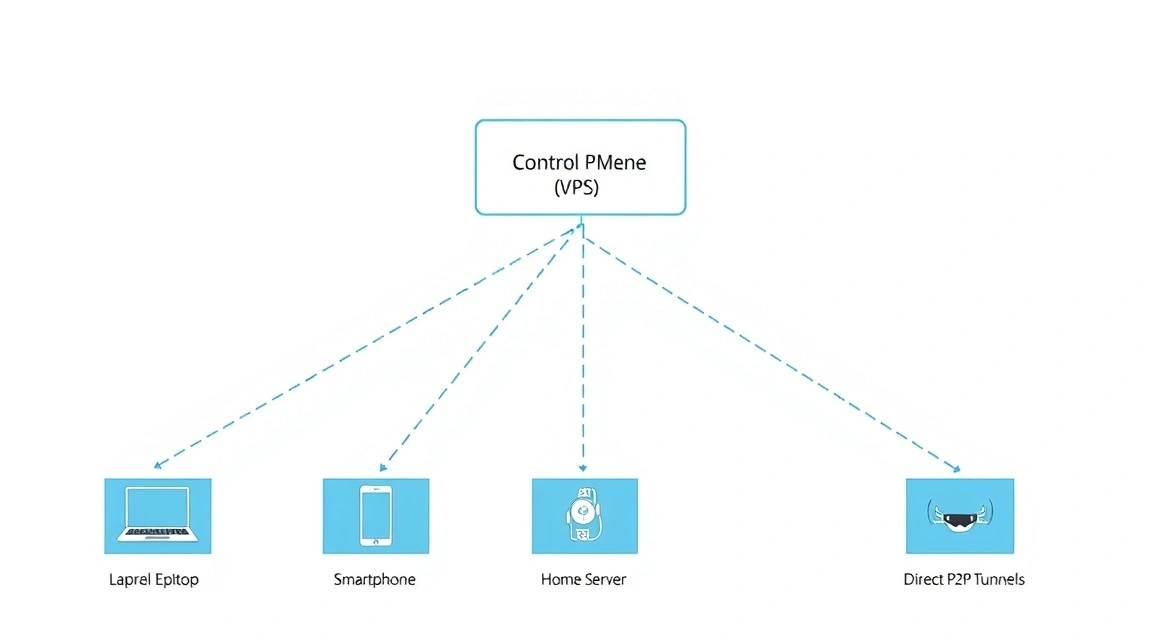 Diagram: 1. What we are setting up and why: The evolution of VPN in 2026
Diagram: 1. What we are setting up and why: The evolution of VPN in 2026
Traditional VPN solutions (OpenVPN, classic WireGuard) work on a "Star" topology. All clients connect to a central server, and all traffic passes through it. This creates a bottleneck: if the server is in Germany and two clients are in Japan, their traffic will still go through Europe, creating huge delays.
Mesh networks solve this problem. In such a network, devices connect directly to each other (point-to-point). A control server is only needed to help devices "find" each other behind NAT and exchange encryption keys. Tailscale popularized this approach using the WireGuard protocol, but their control server is proprietary and cloud-based.
Headscale is a fully open-source implementation of the Tailscale control server. By installing it on your VPS, you get:
- Full privacy: connection logs and keys are stored only by you.
- No limits on the number of devices (Tailscale's free version has limits).
- The ability to configure your own access control rules (ACL).
- Support for MagicDNS — addressing devices by name instead of IP.
In 2026, as digital sovereignty issues become increasingly acute, self-hosted Mesh-VPN is becoming the standard for developers and small businesses.
2. What VPS configuration is needed for Headscale
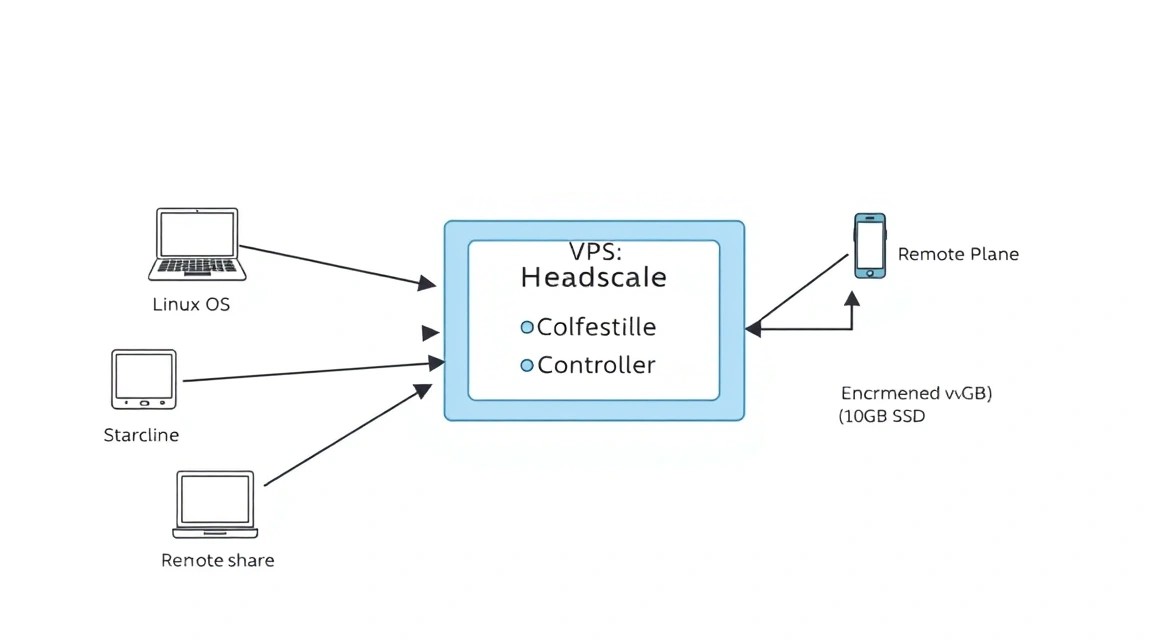 Diagram: 2. What VPS configuration is needed for Headscale
Diagram: 2. What VPS configuration is needed for Headscale
Headscale is an extremely resource-efficient application. Since it only acts as a "coordinator" (Control Plane) and does not proxy all traffic through itself (in most cases), you don't need powerful processors. However, network stability directly depends on the uptime and network connectivity of your provider.
| Parameter |
Minimum Requirements |
Recommended (for teams) |
| Processor (vCPU) |
1 core |
2 cores |
| RAM |
1 GB |
2-4 GB |
| Disk (NVMe SSD) |
10 GB |
40 GB |
| Bandwidth |
100 Mbps |
1 Gbps |
| OS |
Ubuntu 24.04 / Debian 12 |
Ubuntu 24.04 LTS |
For stable operation in Europe or the USA, we recommend using Valebyte. For personal use, the VPS-1 plan (1 vCPU / 2 GB RAM / 30 GB NVMe) for just a few dollars a month is perfect. If you plan to use Headscale as an Exit Node for the whole family or a small company, it's better to choose VPS-2 from Valebyte to have a buffer of RAM for caching and the network stack.
Important: Choose a server location as close as possible to your primary location to minimize latency when establishing the initial connection between nodes.
3. Server Preparation: Security and Basics
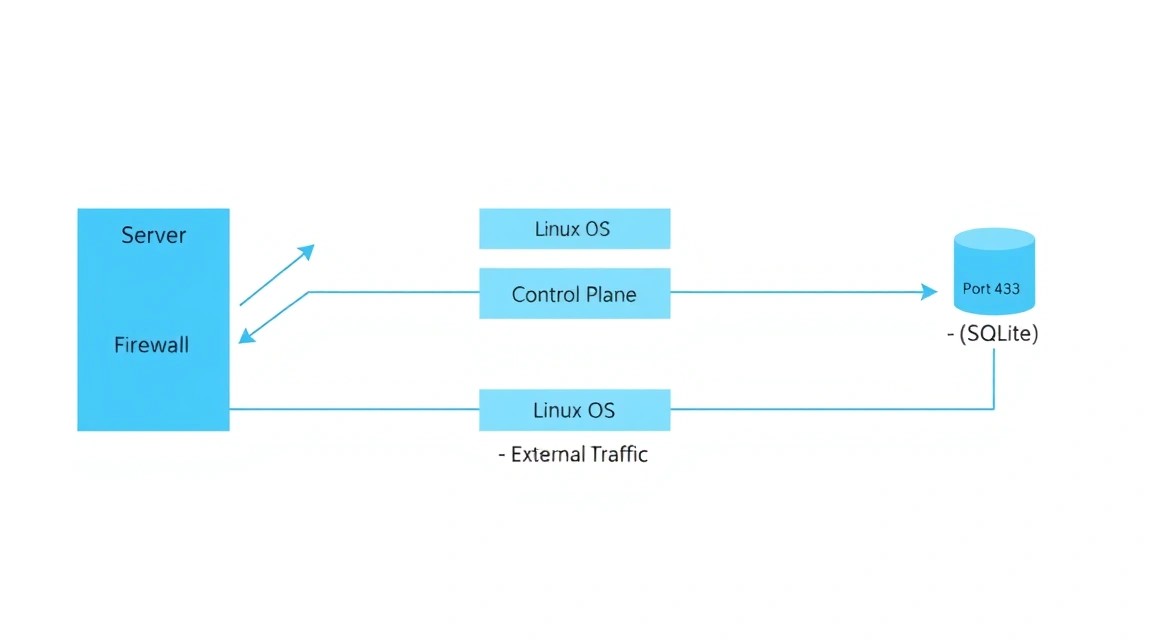 Diagram: 3. Server Preparation: Security and Basics
Diagram: 3. Server Preparation: Security and Basics
Before installing Headscale, it is necessary to provide basic protection for our server. We assume you have a clean server with Ubuntu 24.04.
Let's update the system and install the necessary utilities:
sudo apt update && sudo apt upgrade -y
sudo apt install -y curl wget git vim ufw software-properties-common
Let's configure the firewall. Headscale requires opening a port for coordination (usually 8080 or 443 via proxy) and a port for WireGuard (if you use the built-in DERP server):
# Allow SSH (mandatory!)
sudo ufw allow ssh
# Allow HTTP/HTTPS for Caddy
sudo ufw allow 80/tcp
sudo ufw allow 443/tcp
sudo ufw allow 443/udp
# Enable Firewall
sudo ufw enable
It is recommended to create a separate user with sudo privileges and disable password login for SSH, using only keys. This is the industry standard in 2026 to prevent brute-force attacks.
4. Installing Headscale: A Step-by-Step Algorithm
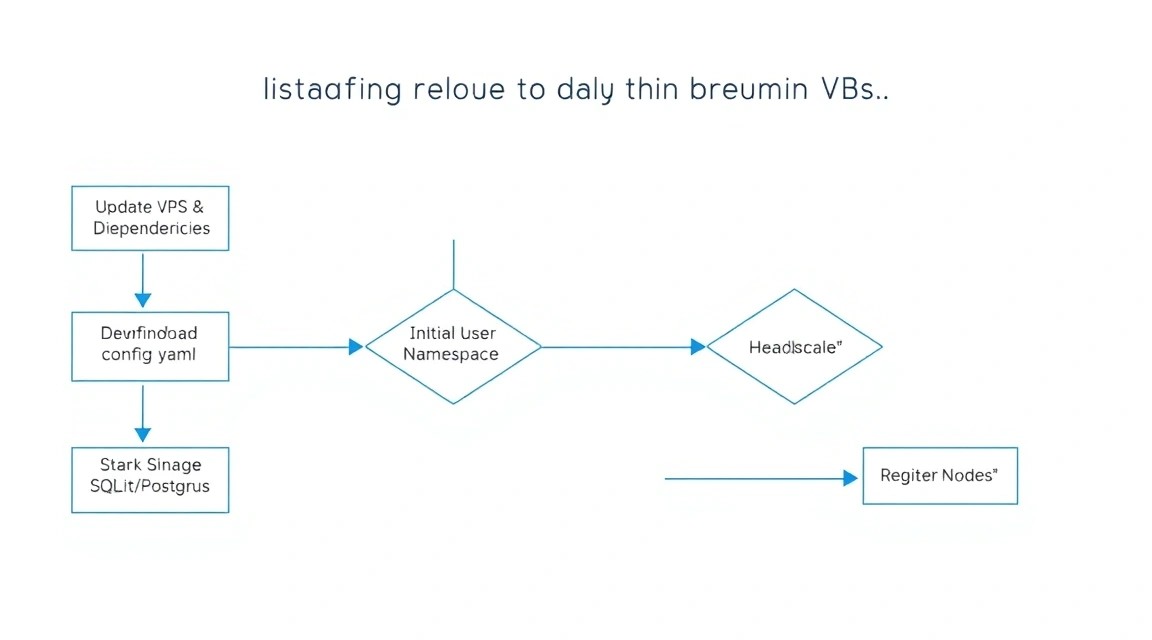 Diagram: 4. Installing Headscale: A Step-by-Step Algorithm
Diagram: 4. Installing Headscale: A Step-by-Step Algorithm
We will use Docker for deployment, as it significantly simplifies the update process and dependency isolation. Let's install Docker and Docker Compose:
# Installing Docker
curl -fsSL https://get.docker.com -o get-docker.sh
sudo sh get-docker.sh
Let's create the directory structure for the project:
mkdir -p ~/headscale/config
mkdir -p ~/headscale/data
cd ~/headscale
Let's create an empty SQLite database file (Headscale uses it by default):
touch ./data/db.sqlite
Now let's create the docker-compose.yaml file. We will use the current Headscale image version 0.23+ (relevant for 2026):
version: '3.8'
services:
headscale:
image: headscale/headscale:latest
container_name: headscale
volumes:
- ./config:/etc/headscale
- ./data:/var/lib/headscale
ports:
- "127.0.0.1:8080:8080"
command: headscale serve
restart: always
Note that we are mapping port 8080 to 127.0.0.1. This is done so that Headscale is not directly accessible from the outside, but only works through our Reverse Proxy (Caddy), which will provide encryption.
5. Configuring Reverse Proxy and SSL (Caddy)
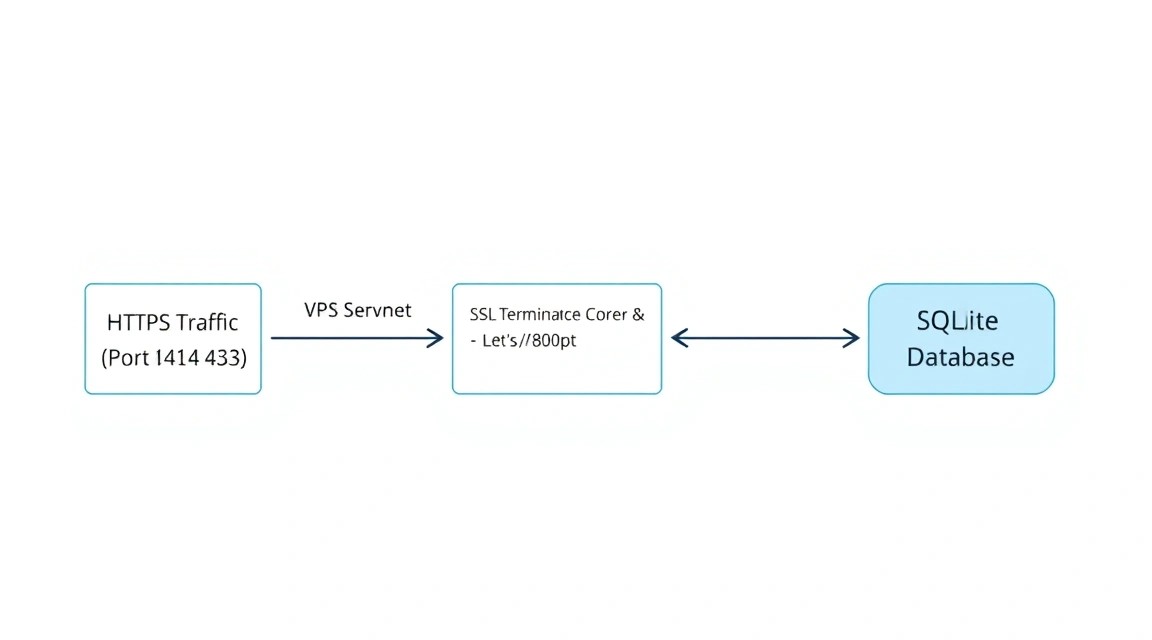 Diagram: 5. Configuring Reverse Proxy and SSL (Caddy)
Diagram: 5. Configuring Reverse Proxy and SSL (Caddy)
Headscale must run over HTTPS. The easiest way to obtain and automatically renew SSL certificates from Let's Encrypt is to use Caddy.
Let's add the Caddy service to our docker-compose.yaml:
caddy:
image: caddy:latest
container_name: caddy
restart: always
ports:
- "80:80"
- "443:443"
- "443:443/udp"
volumes:
- ./Caddyfile:/etc/caddy/Caddyfile
- caddy_data:/data
- caddy_config:/config
volumes:
caddy_data:
caddy_config:
Let's create a Caddyfile in the ~/headscale directory. Replace vpn.yourdomain.com with your actual domain (it must point to the IP of your Valebyte VPS):
vpn.yourdomain.com {
reverse_proxy headscale:8080
}
6. Deep Headscale Configuration
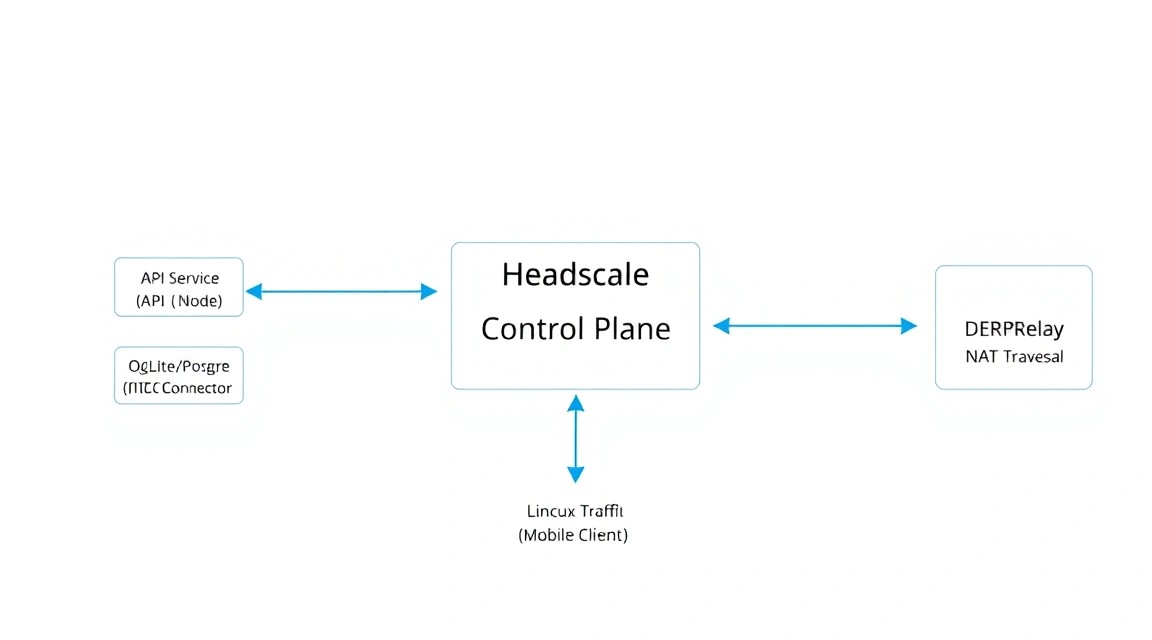 Diagram: 6. Deep Headscale Configuration
Diagram: 6. Deep Headscale Configuration
Now we need to create the main configuration file config.yaml in the ./config folder. You can download a template from the official repository, but here are the key parameters that need to be changed:
# Download the default config
wget https://raw.githubusercontent.com/juanfont/headscale/main/config-example.yaml -O ./config/config.yaml
Edit ./config/config.yaml, paying attention to the following lines:
server_url: https://vpn.yourdomain.com — your external URL.listen_addr: 0.0.0.0:8080 — the address inside the container.ip_prefixes: - 100.64.0.0/10 — standard Tailscale range.magic_dns: true — enabling internal DNS.
After configuration, start the containers:
sudo docker compose up -d
Check the logs to ensure everything started correctly:
sudo docker compose logs -f headscale
7. Connecting Clients (Linux, Windows, Android)
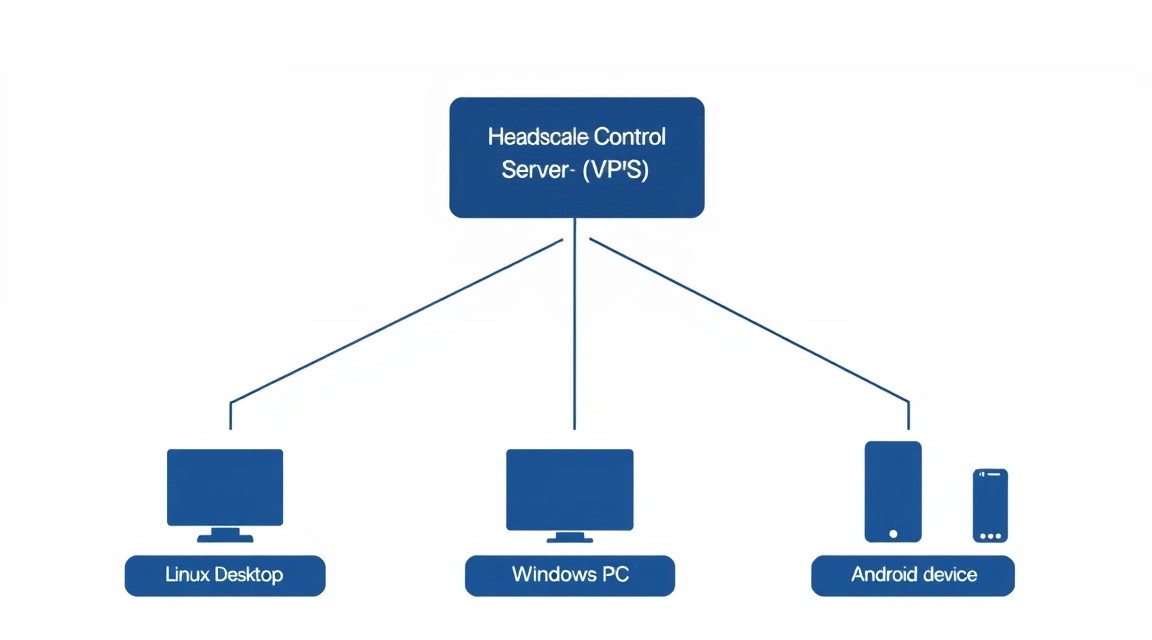 Diagram: 7. Connecting Clients (Linux, Windows, Android)
Diagram: 7. Connecting Clients (Linux, Windows, Android)
To connect devices, you will need the official Tailscale client. However, by default, it attempts to connect to the Tailscale cloud. We need to redirect it to our Headscale.
Creating a User
In Headscale, devices are grouped by users. Let's create the first user "admin":
sudo docker exec headscale headscale users create admin
Connecting a Linux Client
# Install Tailscale
curl -fsSL https://tailscale.com/install.sh | sh
# Authorize in our Headscale
tailscale up --login-server https://vpn.yourdomain.com
The command will output a unique link. Open it (or copy the code) and run the registration command on the server:
sudo docker exec headscale headscale nodes register --user admin --key [YOUR_KEY_FROM_LINK]
Connecting Windows/macOS
For Windows, you need to launch Tailscale and navigate to your control panel address in the browser, or use special registry parameters to change the LoginURL. In 2026, in the Tailscale client, it is sufficient to hold the Alt key while clicking the tray icon to select "Change Server".
Connecting Android/iOS
In the mobile app, you need to quickly tap the "Tailscale" logo in the settings menu 3 times. This will open a hidden "Server URL" field where you should enter https://vpn.yourdomain.com.
8. Backups and System Maintenance
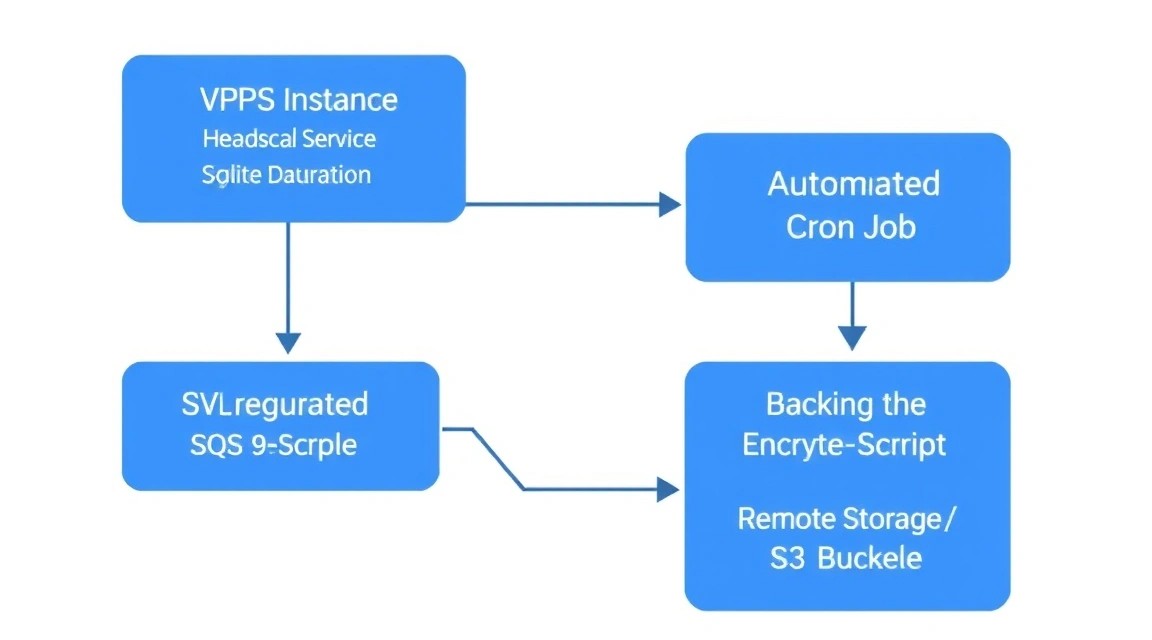 Diagram: 8. Backups and System Maintenance
Diagram: 8. Backups and System Maintenance
Your Headscale server is now a critical point of your infrastructure. If you lose the database, you will have to reconfigure all clients from scratch.
What needs to be backed up:
~/headscale/data/db.sqlite (most important).~/headscale/config/config.yaml.- Server private keys (located in
./config).
Example of a simple backup script (backup.sh):
#!/bin/bash
BACKUP_DIR="/backups/headscale"
TIMESTAMP=$(date +"%Y%m%d_%H%M%S")
mkdir -p $BACKUP_DIR
# Stop the container for DB integrity
docker stop headscale
cp ~/headscale/data/db.sqlite $BACKUP_DIR/db_$TIMESTAMP.sqlite
docker start headscale
# Delete old backups (older than 30 days)
find $BACKUP_DIR -type f -mtime +30 -delete
It is recommended to configure sending these backups to external storage or another VPS from Valebyte for maximum security.
9. Troubleshooting + FAQ
Which error → what to check → how to fix
Problem: Clients cannot see each other (ping fails).
Solution: Check the node status with the headscale nodes list command. Ensure that a strict Firewall blocking WireGuard UDP traffic is not enabled on the clients. Try running tailscale ping [IP_address] to diagnose the path.
Problem: Caddy cannot obtain an SSL certificate.
Solution: Ensure that ports 80 and 443 are open in ufw and that your domain actually points to your VPS IP. Check Let's Encrypt limits.
Which Valebyte config is the minimum suitable?
For Headscale with 10-20 devices, the most basic VPS-1 plan is sufficient. Headscale consumes about 50-100 MB of RAM. The main resource that might be required during active use is network traffic, if you use the server as an Exit Node.
What to choose — VPS or dedicated for this task?
For a Headscale management server, VPS is the ideal choice. A Dedicated server would be overkill, as the CPU will be idle 99% of the time. Dedicated should only be considered if you plan to deploy a powerful DERP relay on the same machine for thousands of simultaneously connected devices with massive traffic.
Can the fact of VPN usage be hidden?
Since Headscale uses WireGuard, its traffic can be identified using DPI. However, thanks to the Mesh structure, most traffic goes directly between your devices, making it difficult to block the entire network. To bypass deep packet inspection in 2026, a combination with Shadowsocks or VLESS is often used.
How to update Headscale?
Simply run:
docker compose pull
docker compose up -d
Docker will automatically update the image to the latest version and restart the container while preserving all data.
10. Conclusions and Next Steps
We have successfully deployed Headscale on a VPS, configured automatic SSL, and connected the first devices. Now you have your own, fully controlled Mesh network that works faster and more stably than traditional VPNs.
Your next steps:
- Configure ACL (Access Control Lists) in
config.yaml to restrict access between devices (for example, to prevent a smartphone from accessing the backup server).
- Set up your own DERP server (Relay) if your devices are often behind strict corporate Firewalls.
- Configure an Exit Node on the Valebyte server to access the internet via the server's IP when you are on public Wi-Fi.
If you haven't chosen a server for your Headscale yet, check out the VPS plans from Valebyte. High NVMe disk speeds and excellent connectivity in Europe will ensure instant connection establishment in your new Mesh network.