Port Scanning and Backdoor Detection: A Guide for System Administrators
Port scanning and backdoor detection are indispensable components in the arsenal of any system administrator striving to ensure robust protection for server infrastructure. Simply put, port scanning allows us to understand which "doors and windows" are open on our servers, while backdoor detection is the process of discovering unauthorized, hidden access points through which attackers can gain or have already gained control over a system. For us, colleagues at Valebyte, where the stability and security of every virtual machine and every physical server are critically important, these practices are not just recommendations, but the foundation of a proactive cybersecurity strategy.
Why is this important for us, Valebyte admins?
We manage a large number of servers, be they dedicated machines or VPS instances. Each of them is a potential target. A compromised server not only jeopardizes client data but can also become a springboard for attacks on other systems in our network, undermine Valebyte's reputation, and lead to serious financial and legal consequences. This is precisely why regular, thoughtful port scanning and methodical backdoor detection are not a luxury, but an urgent necessity. We don't just "maintain" servers; we actively protect them.
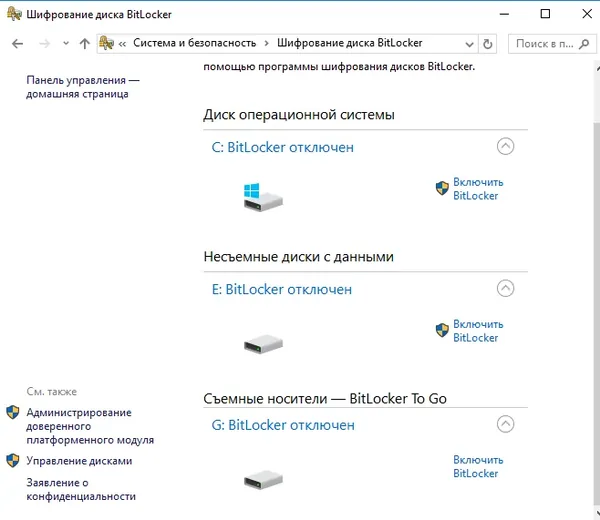
Port Scanning: Auditing Open Doors
Port scanning is a basic but powerful method for assessing a server's attack surface. Essentially, we simulate the actions of a potential attacker, trying to "knock" on various ports to determine which ones are open, what services are behind them, and possibly what versions of those services are running. This helps us identify unwanted or forgotten open ports that could be exploited.
Types of Port Scans and What They Tell Us
- TCP SYN Scan (Half-Open Scan): The most popular and frequently used type. A SYN packet is sent, and if a SYN/ACK is received in response, the port is considered open. Then, an RST packet is sent to prevent a full connection from being established. This makes it relatively "stealthy."
- TCP Connect Scan: Establishes a full three-way TCP handshake. This is less stealthy but reliably works in all conditions and does not require special privileges. Good for simple scripts.
- UDP Scan: Checks UDP ports. Since UDP has no handshake, open ports are harder to determine. The absence of an ICMP "Port Unreachable" response usually indicates an open port, but this is not always reliable.
- FIN/Xmas/Null Scans: More sophisticated methods that use various TCP flags to bypass some firewalls and IDS. They rely on RFC 793, which describes how systems should react to packets with unexpected flags.
- Version Detection: After identifying open ports, Nmap (or similar tools) can attempt to determine the service running on the port and its version. This is critically important, as many vulnerabilities are tied to specific software versions.
- OS Detection: Identifies the operating system running on a remote host by analyzing TCP/IP stack fingerprints.
Tools for Port Scanning
The undisputed king here is Nmap. It's the Swiss Army knife for network auditing and scanning. But there are others that can be useful in specific scenarios.
Nmap: Our Trusted Assistant
Nmap (Network Mapper) is a powerful, flexible, and extensible tool. It doesn't just scan ports; it also provides rich functionality for discovering services, versions, OS, and even executing scripts to identify vulnerabilities.
Examples of Nmap usage:
# Basic SYN scan for a quick overview of open ports
nmap -sS <server_IP_address>
# Scan all ports (1-65535) with service version and OS detection
nmap -p 1-65535 -sV -O <server_IP_address>
# UDP port scan (can be slow)
nmap -sU <server_IP_address>
# Using Nmap Scripting Engine (NSE) to find typical vulnerabilities
# For example, finding anonymous FTP access
nmap --script ftp-anon <server_IP_address>
# Scan an entire subnet
nmap -sS 192.168.1.0/24
# Output results in various formats (XML, Greppable)
nmap -sS -oX output.xml <server_IP_address>
nmap -sS -oG output.gnmap <server_IP_address>
Tip for admins: Always start with Nmap. Its flexibility allows you to adapt scanning to any need, from quick superficial analysis to deep auditing. Don't forget about NSE – it's a powerful tool for automating the search for common vulnerabilities and misconfigurations.
Masscan and Zmap: For Speed
If you need to scan very large IP address ranges or even the entire internet in minutes, Masscan and Zmap are your tools. They are not as detailed as Nmap but are incredibly fast at identifying open ports.
# Masscan example: scanning port 80 on a large subnet
masscan 10.0.0.0/8 -p80 --rate 100000
When to use: When you are running an audit at the data center or large network level and need a quick initial snapshot of open ports. For detailed analysis of a single server, it's better to return to Nmap.
Secure Your Servers from Hidden Threats and Backdoors
Robust protection starts with a secure infrastructure. Choose VPS hosting that helps you prevent unauthorized access. — from €4.49/mo.
Explore VPS Hosting →Backdoor Detection: Finding Hidden Threats
A backdoor is not just an open port. It's a deliberately or accidentally created loophole that allows an attacker to gain access to a system, bypassing normal authentication and security mechanisms. Backdoor detection requires deeper analysis than just port scanning.
How do backdoors manifest themselves?
- Unexpected open ports: Sometimes a backdoor opens its own port that should not be open on the server.
- Hidden processes: Processes that listen on ports but masquerade as legitimate system services or are simply not visible with ordinary commands (if a rootkit is present).
- Modified system files: Replacement or modification of critical system binaries (
ls,netstat,ps,login) to hide activity. - Unauthorized SSH keys: Adding an attacker's public SSH keys to a user's
authorized_keys. - Web Shells: Malicious scripts (PHP, ASP, JSP) uploaded to a web server that provide remote access and the ability to execute commands via a web interface.
- Cron Jobs: Adding malicious commands to
crontabto ensure persistent access or launch malicious software. - Modified configuration files: For example,
/etc/passwd,/etc/sudoers, or service configurations. - Suspicious network traffic: Unusual connections to unknown IP addresses, increased activity, or unexpected protocols.
Backdoor Detection Methodologies
Backdoor detection is a complex process involving both network and host-based analysis.
1. Network Connection and Process Analysis
Start with what's happening "now" on the server.
netstat/ss/lsof: These utilities show active network connections, listening ports, and the processes using them. Look for unknown processes listening on ports, or processes establishing connections to suspicious external IPs.
# List all listening TCP and UDP ports with PID and process name
sudo netstat -tulnp
# Equivalent with ss (faster on systems with many connections)
sudo ss -tulnp
# Which files and sockets are opened by a process (e.g., by PID 1234)
sudo lsof -p 1234
# Which processes are listening on ports
sudo lsof -i -P -n | grep LISTEN
What to look for: Processes that shouldn't be running, processes listening on ports above 1024, unusual connections to external IPs.
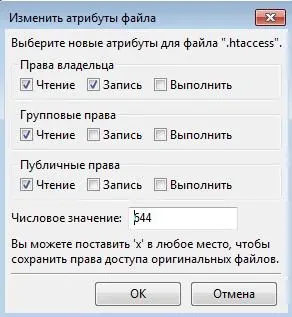
2. File Audit and Integrity Control
Backdoors often leave traces in the file system.
- File Integrity Monitoring (FIM): Tools like AIDE (Advanced Intrusion Detection Environment) or Tripwire create cryptographic hashes of critical system files and configurations. During the next scan, they compare current hashes with baseline ones and report changes. This is the gold standard for detecting modifications.
- Checking recently modified files: Use
findto search for files modified in the last N days, especially in system directories (/bin,/usr/bin,/etc,/var/www).
# Install AIDE (example for Debian/Ubuntu)
sudo apt install aide aide-common
sudo aideinit # Create database
sudo mv /var/lib/aide/aide.db.new /var/lib/aide/aide.db.gz
# Run check
sudo aide --check
# Find files modified in the last 7 days in critical directories
find /etc /bin /usr/bin /usr/sbin /var/www -type f -mtime -7
3. Checking Scheduled Tasks and Autostart
Backdoors aim for persistence.
- Cron Jobs: Check
crontab -lfor each user, as well as files in/etc/cron.*,/etc/crontab. - Systemd Timers: For modern Linux systems, check
systemctl list-timers. - Autostart: Analyze
/etc/rc.local,/etc/init.d/,/etc/systemd/system/and other autostart locations.
4. Rootkit Detection
Rootkits are a set of tools designed to hide an attacker's presence on a system. They can conceal processes, files, and network connections.
- Rkhunter (Rootkit Hunter) and Chkrootkit: These tools scan the system for known rootkits, backdoors, and local exploits by checking system binaries, kernel files, and other suspicious areas.
# Install and run Rkhunter (example for Debian/Ubuntu)
sudo apt install rkhunter
sudo rkhunter --update
sudo rkhunter --check
# Install and run Chkrootkit
sudo apt install chkrootkit
sudo chkrootkit
Important: Rootkits can replace system utilities, so run these scanners from a trusted LiveCD/USB or from a minimally compromised environment.
5. Log Analysis
Logs are the chronicle of events on the server.
- System logs:
/var/log/auth.log(orsecureon RHEL systems) for suspicious login attempts,/var/log/syslog(ormessages) for unusual errors or activity. - Web server logs:
access.loganderror.logfor Apache/Nginx. Look for unusual requests to non-existent files, file upload attempts, abnormally large requests, or requests with suspicious User-Agents. - SIEM/HIDS: Integrated solutions such as OSSEC or Wazuh can centralize log collection and analysis, as well as perform file monitoring and detect rootkits.
6. Checking SSH Keys
One of the simplest ways to install a backdoor is to add one's public key to the ~/.ssh/authorized_keys of the target user.
- Regularly check the contents of
~/.ssh/authorized_keysfor all users, especially forrootand other privileged accounts. Ensure all keys are familiar and authorized.
Proactive Measures and Best Practices
Detection is good, but prevention is better.
- Regular Auditing and Scanning: Automate Nmap scanning of your servers from both the internal network and an external IP. Compare results with previous ones to identify new open ports.
- Minimize Attack Surface: Close all ports that are not absolutely necessary. Disable unnecessary services. Apply the principle of least privilege.
- Up-to-date Software: Regularly update operating systems and all installed software. Most backdoors and exploits use known vulnerabilities.
- Robust Firewalls: Use both network firewalls (e.g., iptables/ufw) and host-level firewalls. Configure them based on the "deny all that is not explicitly permitted" principle.
- Intrusion Detection/Prevention Systems (IDS/IPS): Install and configure IDS/IPS to monitor network traffic for anomalies and known attack signatures.
- File Integrity Monitoring (FIM): Use AIDE or Tripwire to track changes in critical files.
- Centralized Log Collection and Analysis (SIEM): Implement a solution for centralized log collection, such as ELK Stack, Graylog, or Wazuh, to simplify anomaly detection.
- Strong Password and SSH Key Policy: Use complex passwords, disable password authentication for SSH, using only SSH keys. Regularly check
authorized_keys. - Network Segmentation: Divide the network into smaller, isolated segments. This will help contain the spread of an attack in case one server is compromised.
- Backup: Regular creation and verification of working backups allow for quick recovery after an incident.
Conclusion
Port scanning and backdoor detection are not one-time tasks but a continuous process requiring vigilance, methodicalness, and constant learning. As system administrators at Valebyte, we are responsible for the security of our systems and our clients' data. Actively applying the described methods and tools, combined with a proactive approach to security, will allow us to significantly reduce risks and promptly respond to potential threats. Remember, security is a marathon, not a sprint. Be vigilant and continuously improve your skills.
Maximum Security and Flexibility for Your Applications
Need a scalable and secure environment? Our cloud instances offer the ideal solution for threat detection and data protection.
Start with Cloud →