Server Security [EN]
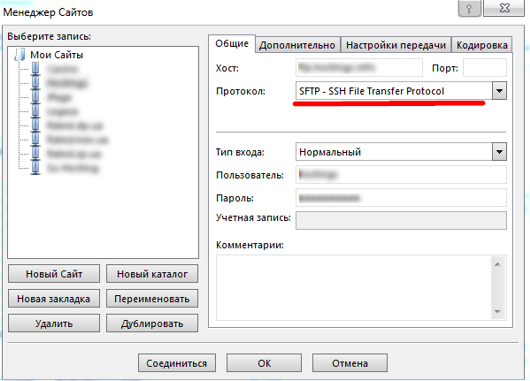
How to Secure Your FTP Server: Essential Security Tips
How to Secure an FTP Server? An FTP server is one of the most common means of transferring files. However,…
Read More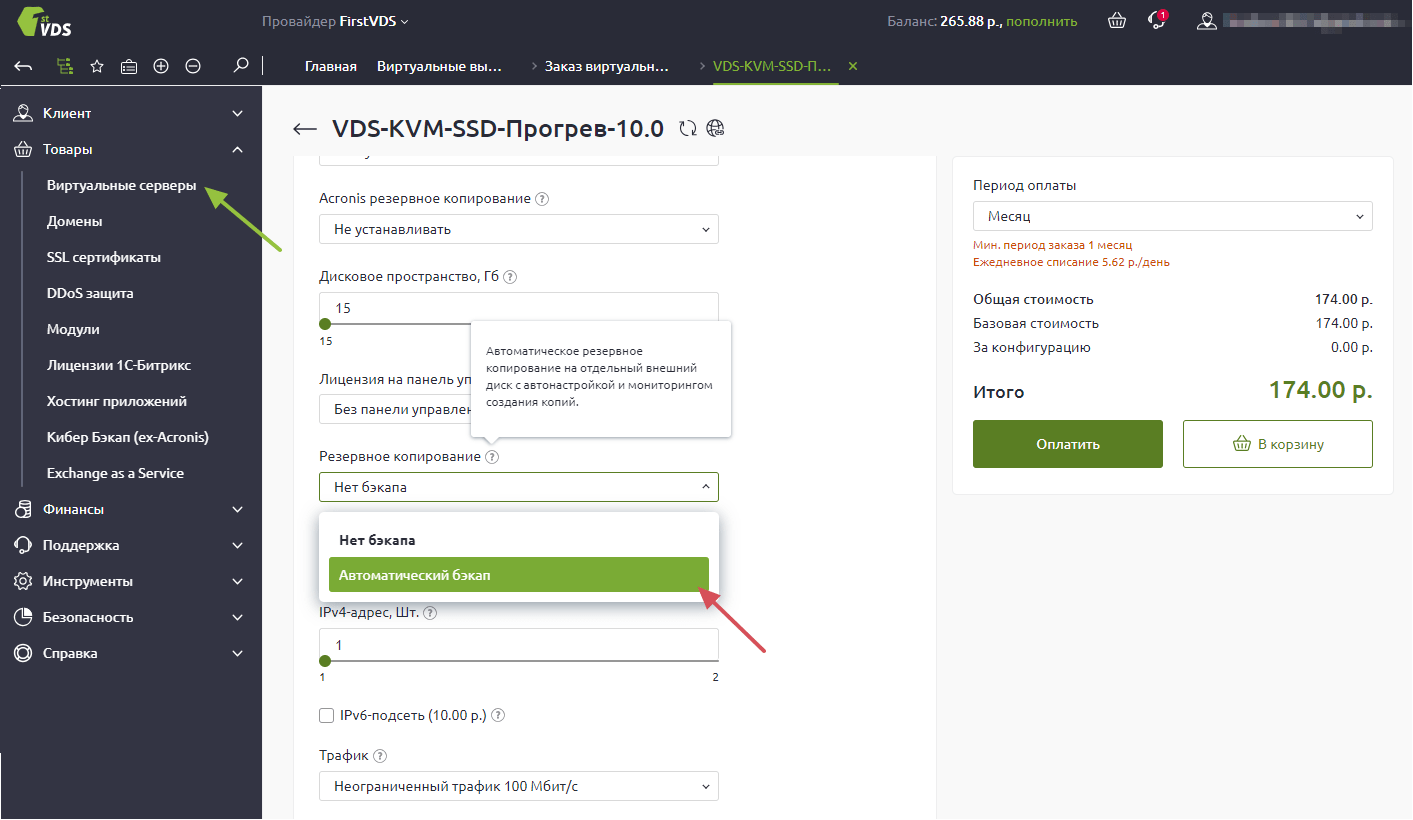
How to Set Up Automated Server Backups: A Complete Guide
How to Set Up Automatic Server Backup? Data security is one of the key aspects of server operation. Creating regular…
Read More
How to Secure Your MySQL Server from Hackers: Top Security Tips
How to Protect Your MySQL Server from Hacking? The MySQL server is one of the most popular relational databases, used…
Read More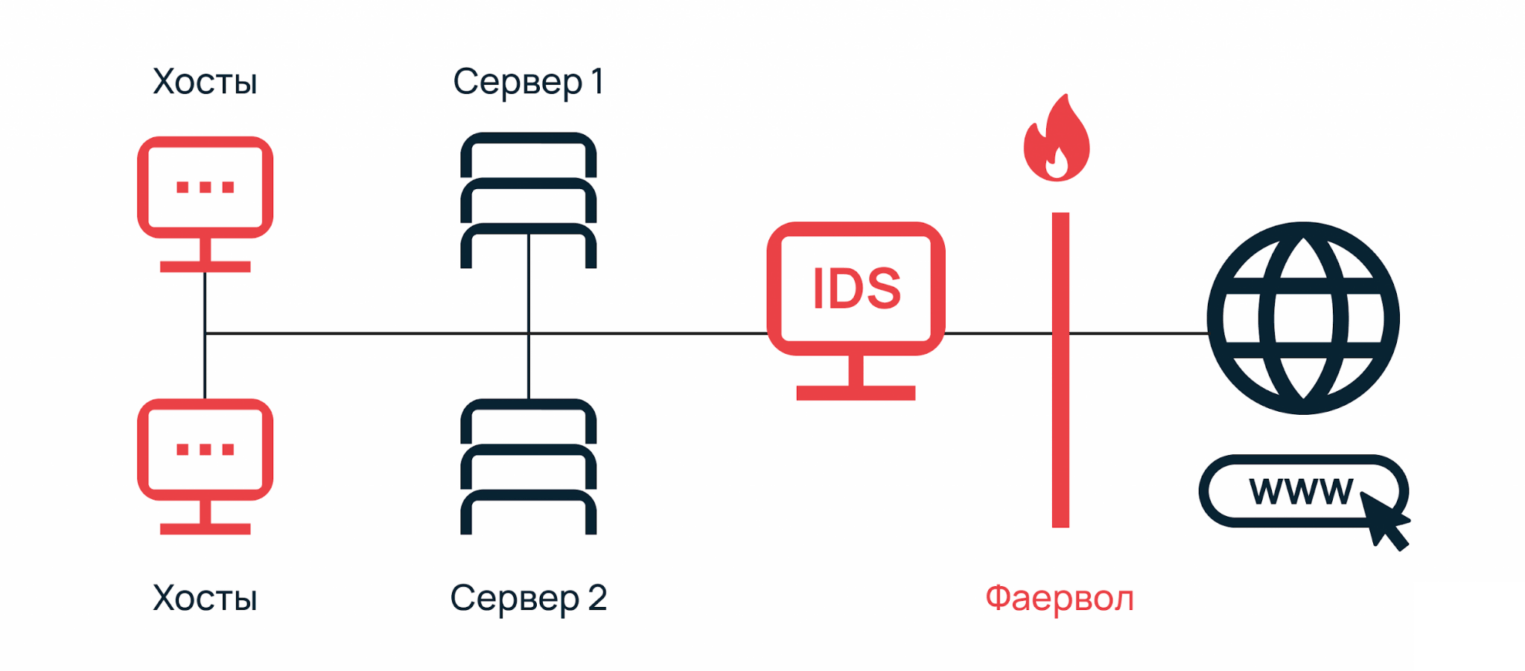
How to Set Up Your Intrusion Detection and Prevention System (IDS/IPS)
How to Set Up an IDS/IPS System? IDS and IPS are security tools that can help protect your network from…
Read More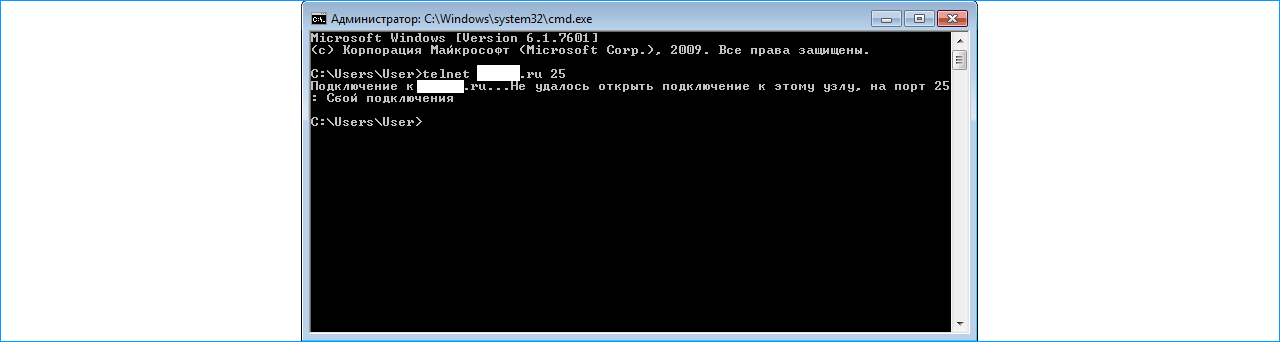
How to Check if a Port is Open on Your Server
How to Check if a Port is Open on a Server? When you’re managing a server, it’s important to know…
Read More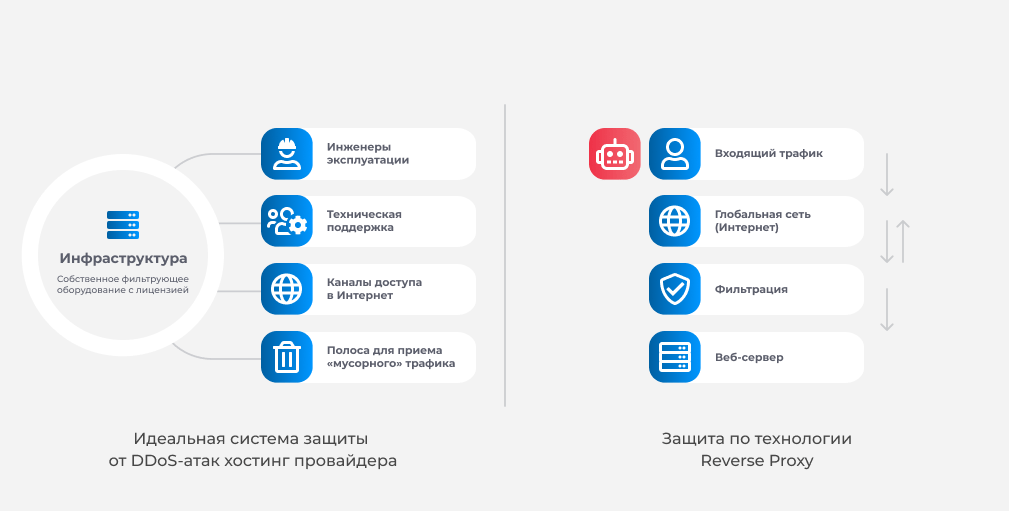
Which Hosting Providers Offer DDoS Protection?
Which Hosting Providers Offer Protection Against Attacks? In our time, cybersecurity plays an extremely important role. With the growth of…
Read More
How to Protect Your Web Server from Bots: Effective Strategies
«`html How to Protect a Web Server from Bots? How to Protect a Web Server from Bots? Many web server…
Read More
How to Set Up a Firewall on Your Linux Server: A Comprehensive Guide
How to Configure a Firewall on a Linux Server? A firewall is a program designed to protect a computer or…
Read More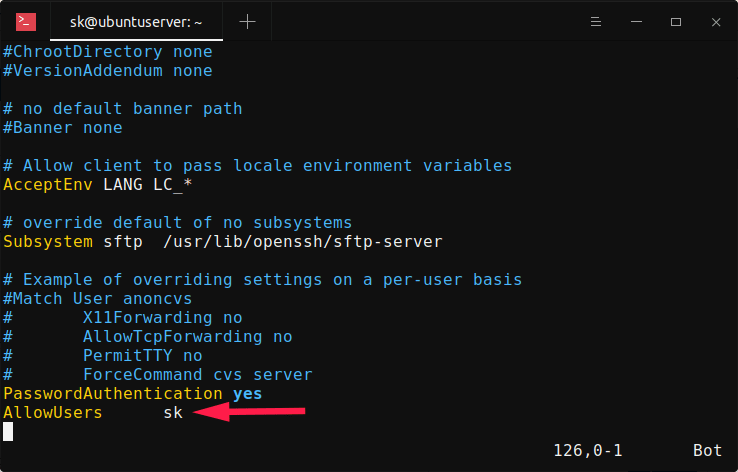
How to Restrict SSH Access to a Single IP Address
«`html How to Restrict SSH Access to Only One IP? How to Restrict SSH Access to Only One IP? SSH…
Read More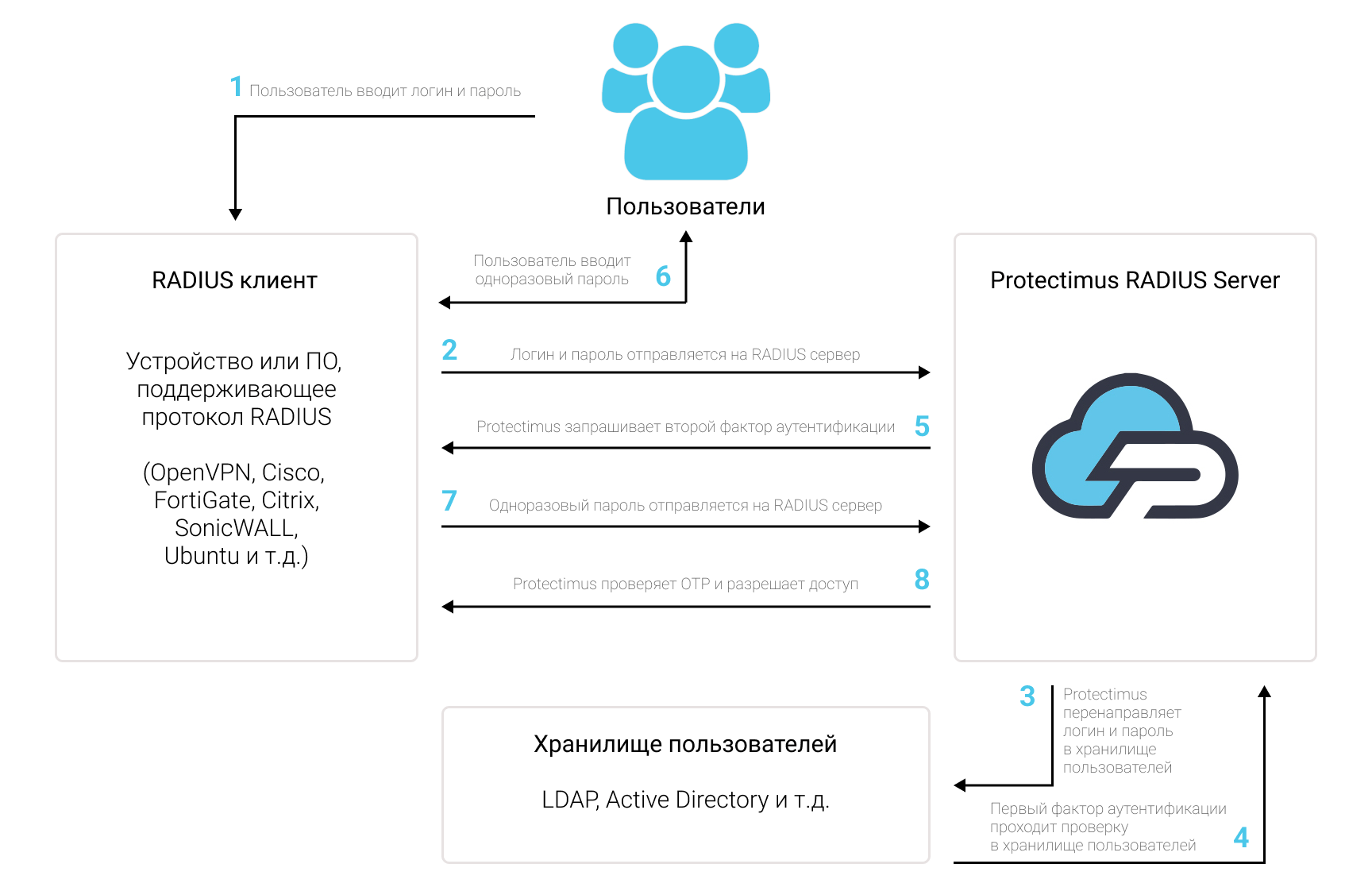
How to Enable Two-Factor Authentication (2FA) on Your Server
«`html How to Use Two-Factor Authentication on Your Server? How to Use Two-Factor Authentication on Your Server? Two-factor authentication is…
Read MoreSearch
Recent Posts
- How to Test Your VDS Windows Hard Drive Speed? 18.11.2025
- How to Install and Configure Fail2ban on Ubuntu VPS: A Step-by-Step Guide 18.11.2025
- How to Configure Nagios Alerts on a Dedicated Server: A Step-by-Step Guide 17.11.2025
- How to View Running Processes on a Linux Ubuntu VPS in 2025 17.11.2025
- Simple Script to Monitor VDS Disk Space (and Avoid Running Out!) 16.11.2025
Categories
- Backups & Data Recovery [EN] (64)
- Backups & Recovery [EN] (1)
- Backups and Data Recovery [EN] (65)
- Backups and Recovery [EN] (2)
- Data Backup & Recovery [EN] (18)
- Data Backup and Recovery [EN] (19)
- Guides and Tutorials [EN] (1)
- Internet Security [EN] (12)
- Performance & Optimization [EN] (30)
- Server Monitoring & Management [EN] (91)
- Server Monitoring and Management [EN] (44)
- Server Security [EN] (129)
- Software & Tools [EN] (13)
- Tech Support & Troubleshooting [EN] (79)
- Technical Support [EN] (79)
- Technical Support & Troubleshooting [EN] (7)
- Troubleshooting [EN] (36)
- VPS & Virtualization [EN] (201)
- VPS and virtualization [EN] (1)
- VPS VDS RDP [EN] (12)
- VPS/VDS/RDP [EN] (93)
- Мониторинг и управление сервером [RU] [EN] (54)
- Техническая поддержка и устранение проблем [EN] (1)
