Server Security [EN]

How to Stop Brute-Force Attacks: Server Security Tips
How to Protect Your Server from Brute-Force Attacks? Brute-force is an attack method where malicious actors attempt to compromise a…
Read More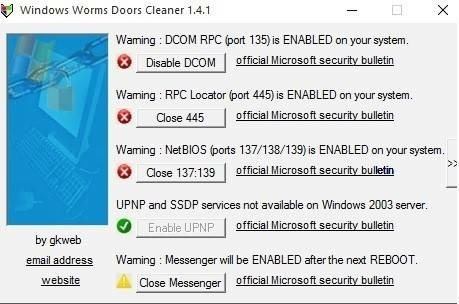
Which Server Ports Should You Close for Enhanced Security?
Which Ports Should You Close on Your Server? Closing unnecessary ports on a server is an important security measure. Open…
Read More
How to Protect Your Server from Malware: Essential Security Tips
How to Protect Your Server from Malware? Servers are a key element of any IT infrastructure. They store and process…
Read More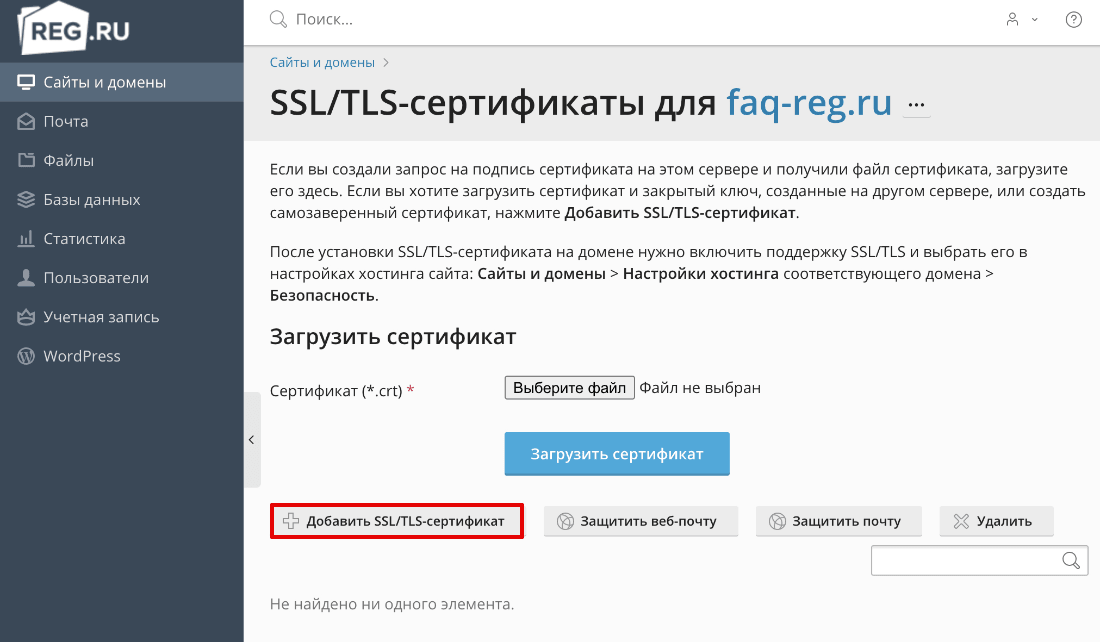
How to Install an SSL/TLS Certificate on Your Server: A Step-by-Step Guide
How to Install an SSL/TLS Certificate on a Server? SSL (Secure Sockets Layer) and its subsequent evolution TLS (Transport Layer…
Read More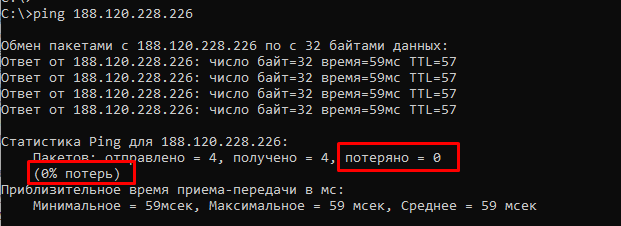
Who’s Connected to My Server? A Quick Check Guide
How to Check Who is Connected to the Server? When you have a server, it is very important to know…
Read More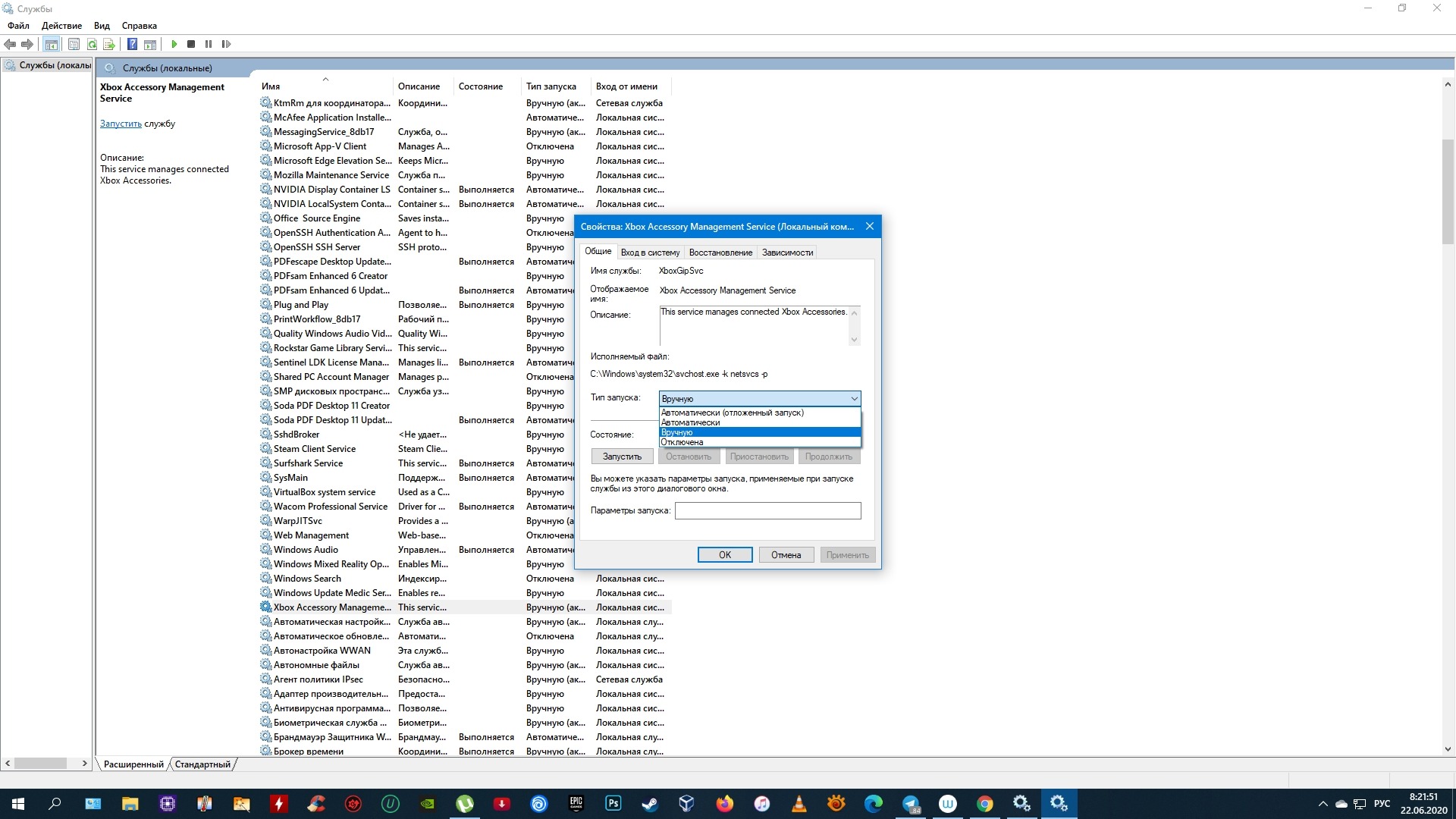
How to Disable Unnecessary Services on Your Server: A Guide to Boosting Performance & Security
How to Disable Unnecessary Services on a Server? Whether it’s a web server, database, or any other software, servers often…
Read More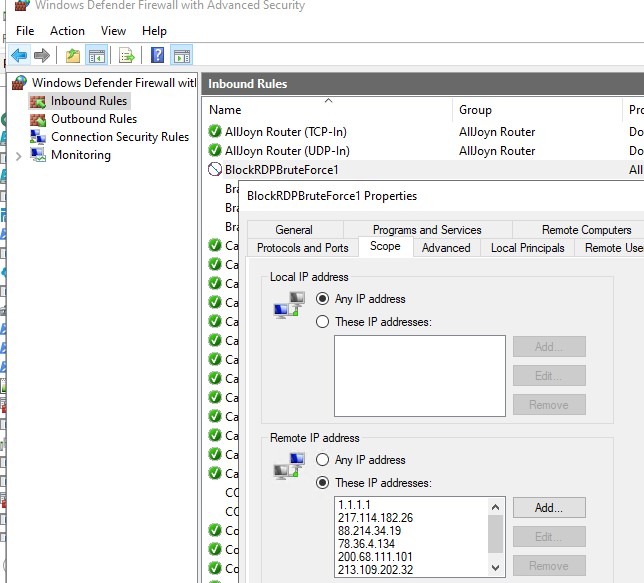
How to Stop Brute-Force Attacks: Securing Your Server
How to Protect Your Server from Password Brute-Force Attacks? Password brute-forcing is one of the most common methods of attacking…
Read More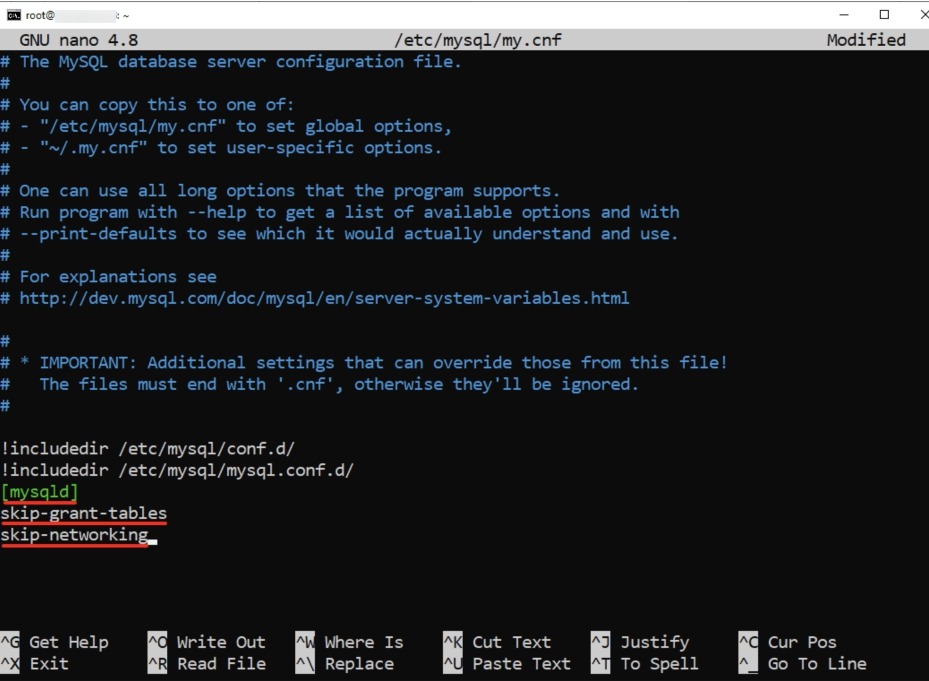
How to Remove Root Access in MySQL: A Step-by-Step Guide
How to Remove Root Access in MySQL? The root user in MySQL has virtually unlimited rights, so the security of…
Read More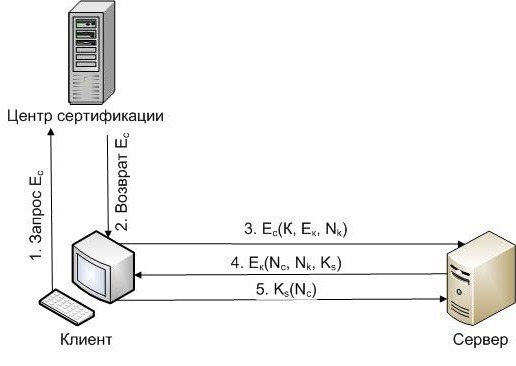
How to Encrypt Client-Server Traffic: A Complete Guide
How to Encrypt Traffic Between Client and Server? Protecting data on the internet is becoming increasingly important these days, especially…
Read More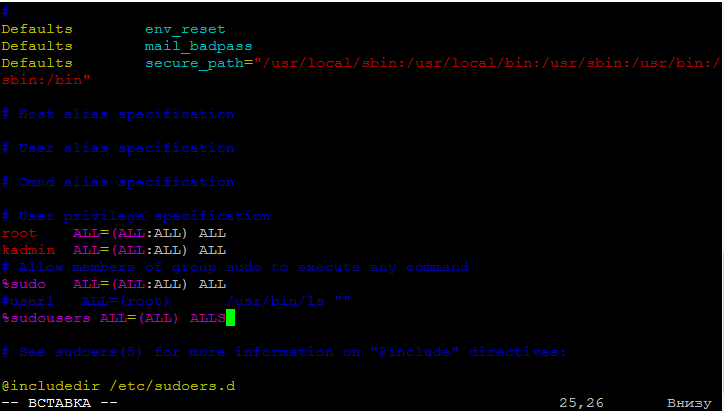
How to Restrict Sudo Access: Enhanced Security Guide
How to Restrict Sudo Access? sudo is a utility for executing commands as another user. It’s very convenient, but it’s…
Read MoreSearch
Recent Posts
- How to Test Your VDS Windows Hard Drive Speed? 18.11.2025
- How to Install and Configure Fail2ban on Ubuntu VPS: A Step-by-Step Guide 18.11.2025
- How to Configure Nagios Alerts on a Dedicated Server: A Step-by-Step Guide 17.11.2025
- How to View Running Processes on a Linux Ubuntu VPS in 2025 17.11.2025
- Simple Script to Monitor VDS Disk Space (and Avoid Running Out!) 16.11.2025
Categories
- Backups & Data Recovery [EN] (64)
- Backups & Recovery [EN] (1)
- Backups and Data Recovery [EN] (65)
- Backups and Recovery [EN] (2)
- Data Backup & Recovery [EN] (18)
- Data Backup and Recovery [EN] (19)
- Guides and Tutorials [EN] (1)
- Internet Security [EN] (12)
- Performance & Optimization [EN] (30)
- Server Monitoring & Management [EN] (91)
- Server Monitoring and Management [EN] (44)
- Server Security [EN] (129)
- Software & Tools [EN] (13)
- Tech Support & Troubleshooting [EN] (79)
- Technical Support [EN] (79)
- Technical Support & Troubleshooting [EN] (7)
- Troubleshooting [EN] (36)
- VPS & Virtualization [EN] (201)
- VPS and virtualization [EN] (1)
- VPS VDS RDP [EN] (12)
- VPS/VDS/RDP [EN] (93)
- Мониторинг и управление сервером [RU] [EN] (54)
- Техническая поддержка и устранение проблем [EN] (1)
