Server Security [EN]

Prevent SQL Injection: Securing Your Server
How to Protect Your Server from SQL Injection Attacks? SQL injection is one of the most common methods of attacking…
Read More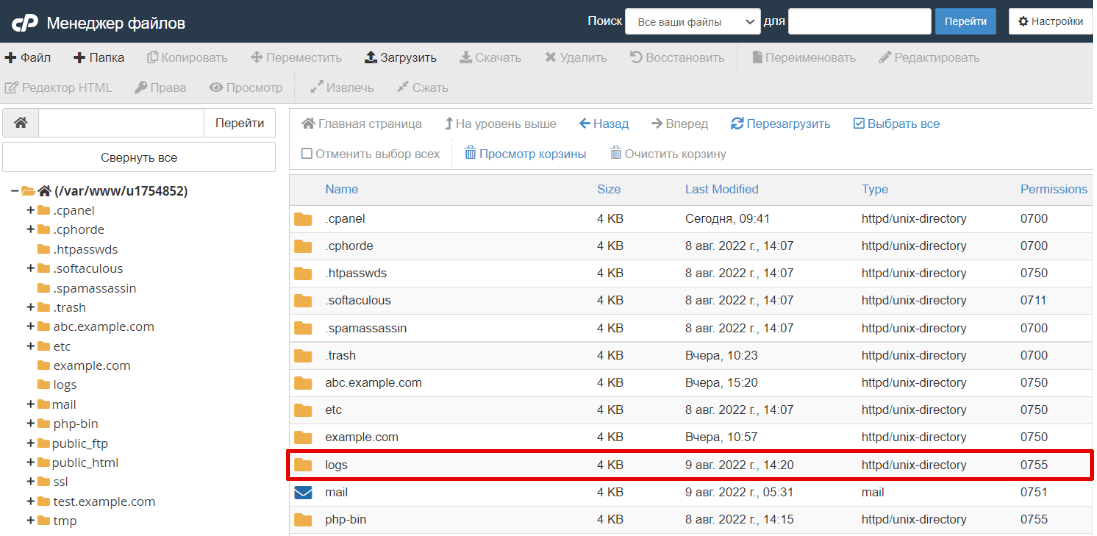
Essential Server Logs to Monitor for Optimal Performance
What Logs Should You Monitor on Your Server? Logs are an integral part of any server. They contain valuable information…
Read More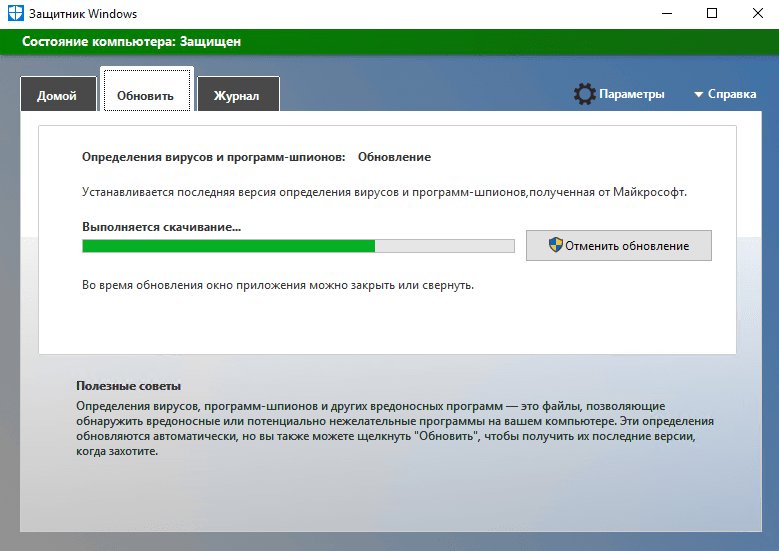
How to Install Antivirus on a Server: A Step-by-Step Guide
How to Install Antivirus on a Server? Antivirus software on a server is a necessity in our modern world, where…
Read More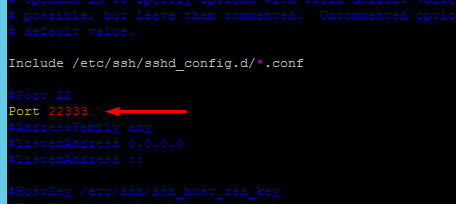
Disable SSH Password Authentication: Enhance Security
How to Disable SSH Password Authentication? SSH is a protocol that enables secure communication and access to a remote server.…
Read More
Securing Your System: AppArmor vs. SELinux — Which One’s Right for You?
«`html How to Use AppArmor or SELinux for Security? AppArmor and SELinux are two of the most popular security systems…
Read More
How to Scan for Rootkits: A Comprehensive Guide
How to Check Files for Rootkits? Rootkits are malicious programs that can hide their presence and actions on an infected…
Read More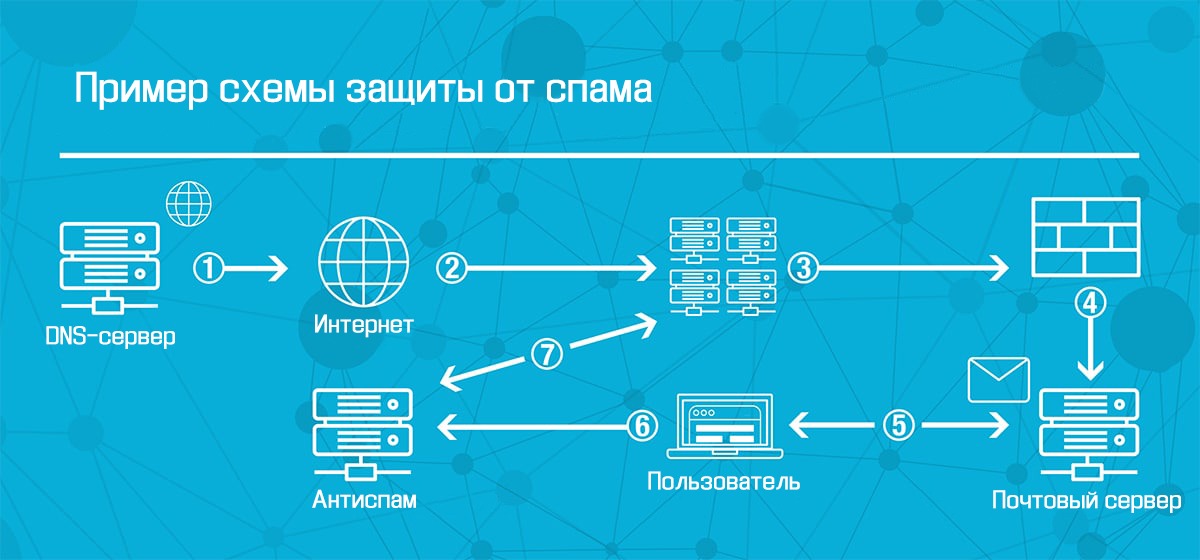
How to Protect Your Email Server from Spam: Proven Techniques
How to Protect Your Mail Server from Spam? Spam is a constant headache for email server administrators. It clutters user…
Read More
How to Encrypt Data on Your Server: A Comprehensive Guide
How to Encrypt Data on a Server? Protecting data on a server plays a crucial role in ensuring information security.…
Read More
How to Use chroot for User Isolation: A Practical Guide
How to Use chroot for User Isolation? Chroot is a handy and effective tool for isolating users on Unix-like systems.…
Read MoreHow to Verify File Integrity on Your Server: A Comprehensive Guide
How to Check File Integrity on a Server? When working with websites, it’s essential to ensure the security and integrity…
Read MoreSearch
Recent Posts
- How to Test Your VDS Windows Hard Drive Speed? 18.11.2025
- How to Install and Configure Fail2ban on Ubuntu VPS: A Step-by-Step Guide 18.11.2025
- How to Configure Nagios Alerts on a Dedicated Server: A Step-by-Step Guide 17.11.2025
- How to View Running Processes on a Linux Ubuntu VPS in 2025 17.11.2025
- Simple Script to Monitor VDS Disk Space (and Avoid Running Out!) 16.11.2025
Categories
- Backups & Data Recovery [EN] (64)
- Backups & Recovery [EN] (1)
- Backups and Data Recovery [EN] (65)
- Backups and Recovery [EN] (2)
- Data Backup & Recovery [EN] (18)
- Data Backup and Recovery [EN] (19)
- Guides and Tutorials [EN] (1)
- Internet Security [EN] (12)
- Performance & Optimization [EN] (30)
- Server Monitoring & Management [EN] (91)
- Server Monitoring and Management [EN] (44)
- Server Security [EN] (129)
- Software & Tools [EN] (13)
- Tech Support & Troubleshooting [EN] (79)
- Technical Support [EN] (79)
- Technical Support & Troubleshooting [EN] (7)
- Troubleshooting [EN] (36)
- VPS & Virtualization [EN] (201)
- VPS and virtualization [EN] (1)
- VPS VDS RDP [EN] (12)
- VPS/VDS/RDP [EN] (93)
- Мониторинг и управление сервером [RU] [EN] (54)
- Техническая поддержка и устранение проблем [EN] (1)
