Server Security [EN]
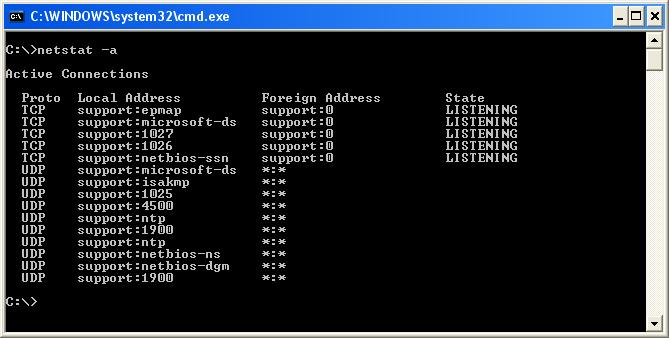
How to Check Your Server for Open Ports: A Security Guide
How to Check a Server for Open Ports? Checking a server for open ports is an important step in ensuring…
Read More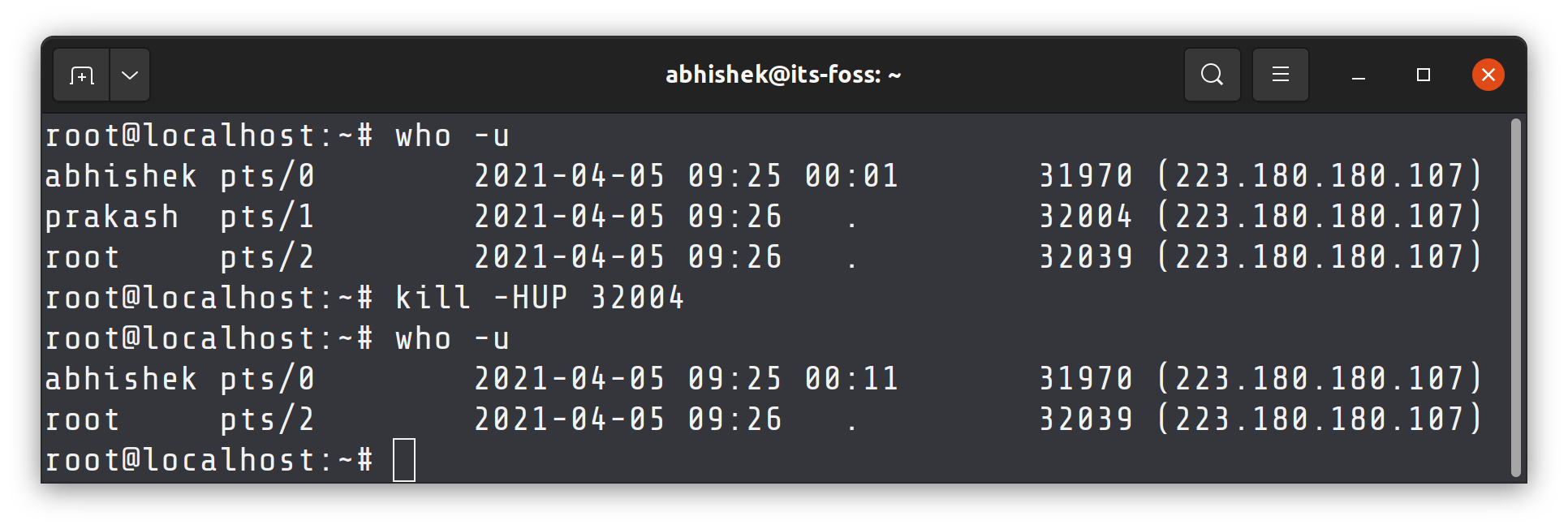
Secure Your SSH: How to Enable Automatic Logout
How to Enable Automatic Logout for SSH? SSH (Secure Shell) is a cryptographic network protocol that provides a secure connection…
Read More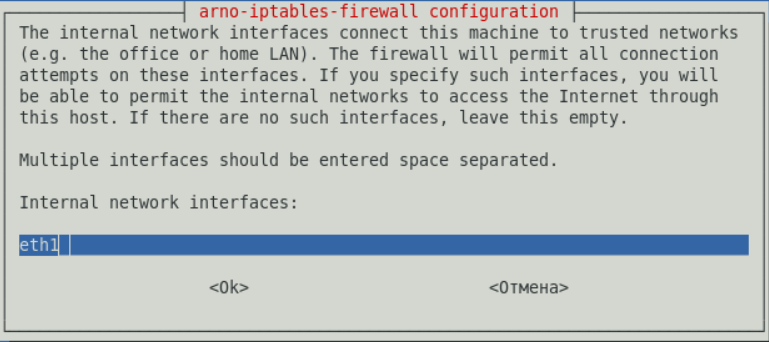
How to Secure Your Server: A Step-by-Step Guide to iptables Configuration
How to Configure iptables to Protect Your Server? Welcome to our guide on configuring iptables to ensure the security of…
Read More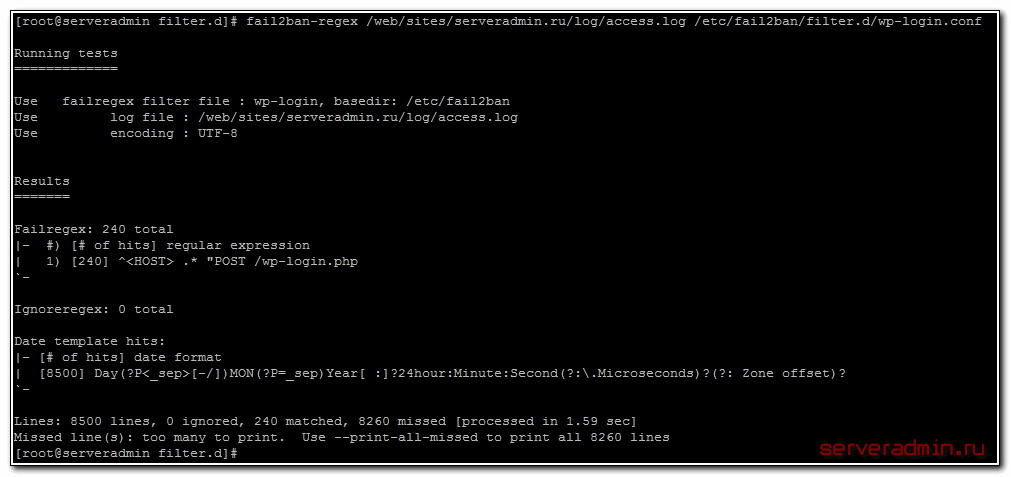
How to Secure WordPress with Fail2Ban: A Step-by-Step Guide
How to Configure Fail2Ban to Protect WordPress? WordPress is a popular platform for creating websites, which is susceptible to hacker…
Read More
How to Protect Your Server from Malicious Scripts: Essential Security Tips
How to Protect Your Server from Malicious Scripts? Maintaining server security is crucial for any web resource owner. Malicious scripts…
Read More
How to Scan Your Server for Security Vulnerabilities: A Step-by-Step Guide
How to Check for Vulnerabilities on Your Server? In our time, cybersecurity plays a huge role. It is especially important…
Read More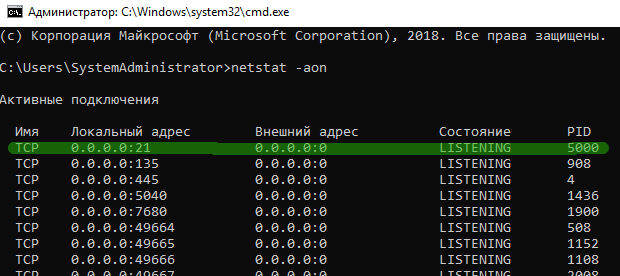
How to Check Which Ports a Server is Listening On
How to Find Out Which Ports a Server is Listening On? Knowing which ports your server is listening on can…
Read More
Best Security Monitoring Tools to Protect Your Business
What Security Monitoring Tools Should You Use? Security plays a huge role in today’s world, especially in the digital space.…
Read More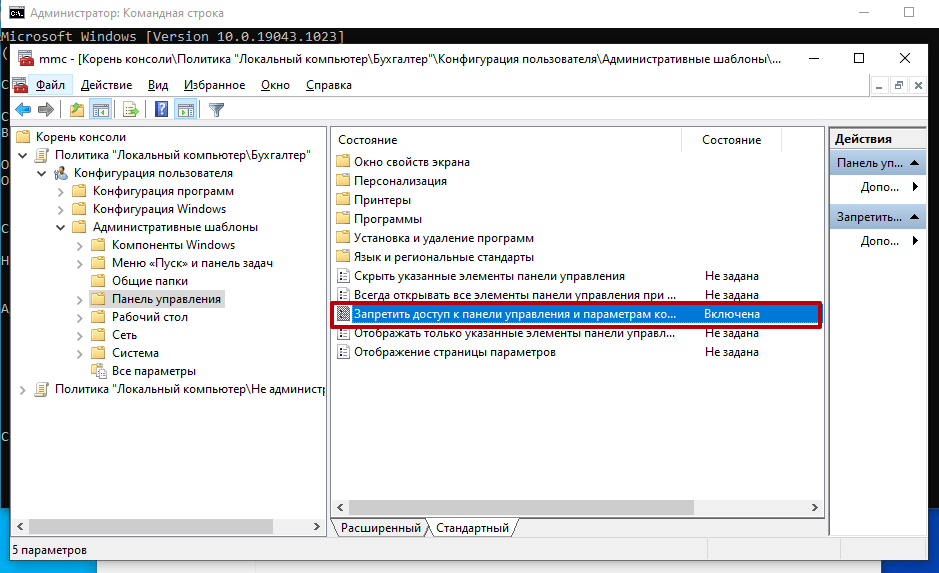
How to Restrict Access to Your Server Control Panel: Enhanced Security Guide
«`html How to Restrict Access to the Server Control Panel? How to Restrict Access to the Server Control Panel? If…
Read More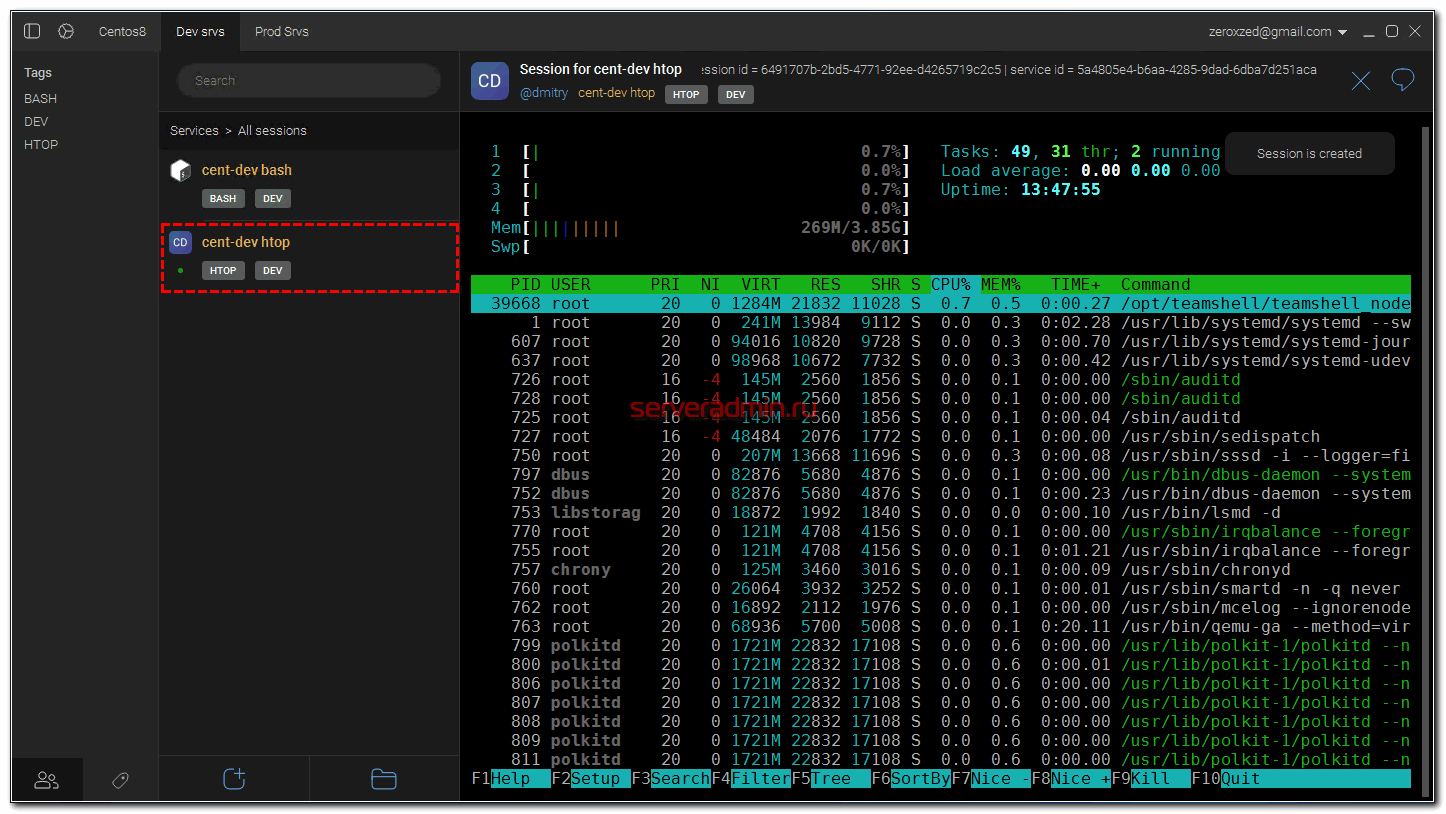
Secure Your Server: How to Log All SSH Connections
How to Configure Logging of All SSH Connections? SSH (Secure Shell) is one of the most popular protocols for remote…
Read MoreSearch
Recent Posts
- How to Test Your VDS Windows Hard Drive Speed? 18.11.2025
- How to Install and Configure Fail2ban on Ubuntu VPS: A Step-by-Step Guide 18.11.2025
- How to Configure Nagios Alerts on a Dedicated Server: A Step-by-Step Guide 17.11.2025
- How to View Running Processes on a Linux Ubuntu VPS in 2025 17.11.2025
- Simple Script to Monitor VDS Disk Space (and Avoid Running Out!) 16.11.2025
Categories
- Backups & Data Recovery [EN] (64)
- Backups & Recovery [EN] (1)
- Backups and Data Recovery [EN] (65)
- Backups and Recovery [EN] (2)
- Data Backup & Recovery [EN] (18)
- Data Backup and Recovery [EN] (19)
- Guides and Tutorials [EN] (1)
- Internet Security [EN] (12)
- Performance & Optimization [EN] (30)
- Server Monitoring & Management [EN] (91)
- Server Monitoring and Management [EN] (44)
- Server Security [EN] (129)
- Software & Tools [EN] (13)
- Tech Support & Troubleshooting [EN] (79)
- Technical Support [EN] (79)
- Technical Support & Troubleshooting [EN] (7)
- Troubleshooting [EN] (36)
- VPS & Virtualization [EN] (201)
- VPS and virtualization [EN] (1)
- VPS VDS RDP [EN] (12)
- VPS/VDS/RDP [EN] (93)
- Мониторинг и управление сервером [RU] [EN] (54)
- Техническая поддержка и устранение проблем [EN] (1)
