Server Security [EN]
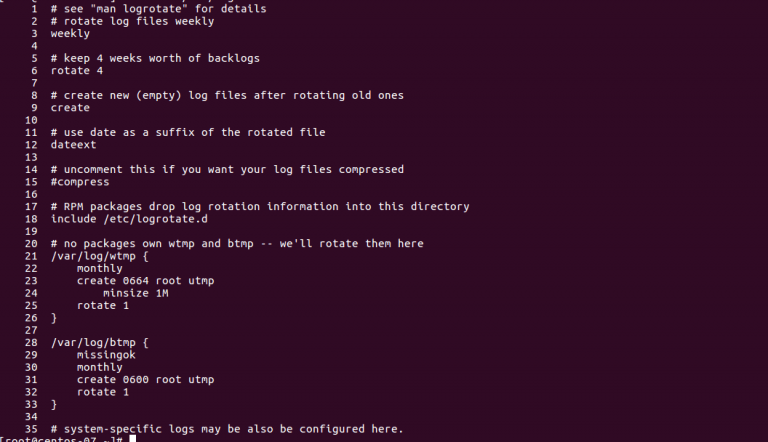
Logrotate Configuration for Enhanced Security: A Comprehensive Guide
How to Configure logrotate for Security? Logs are an essential tool for tracking activity on your system. However, if you…
Read More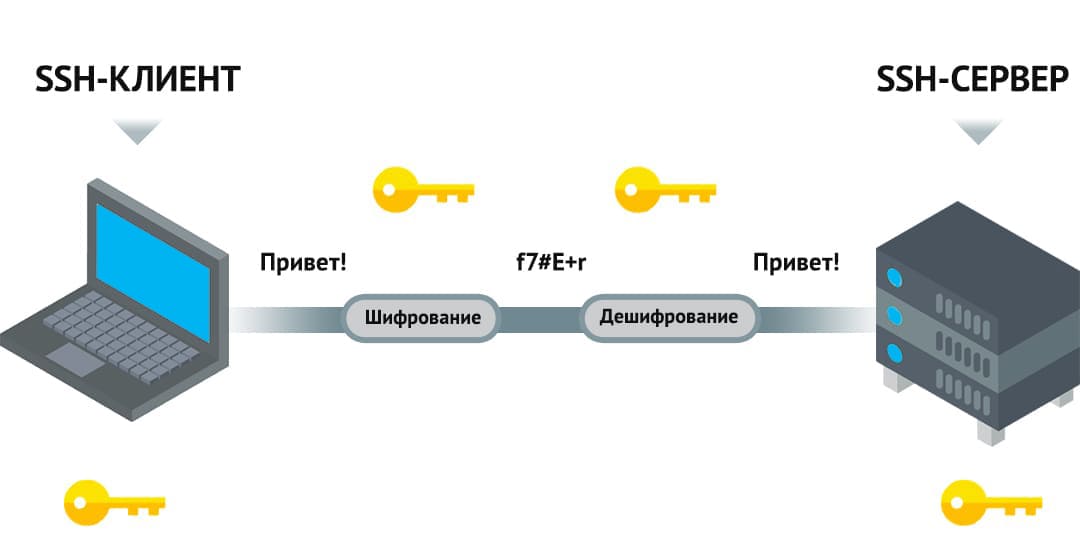
How to Protect Your Server from Traffic Sniffing Attacks
How to Protect Your Server from Traffic Interception? Traffic interception is one of the most serious threats to a server.…
Read More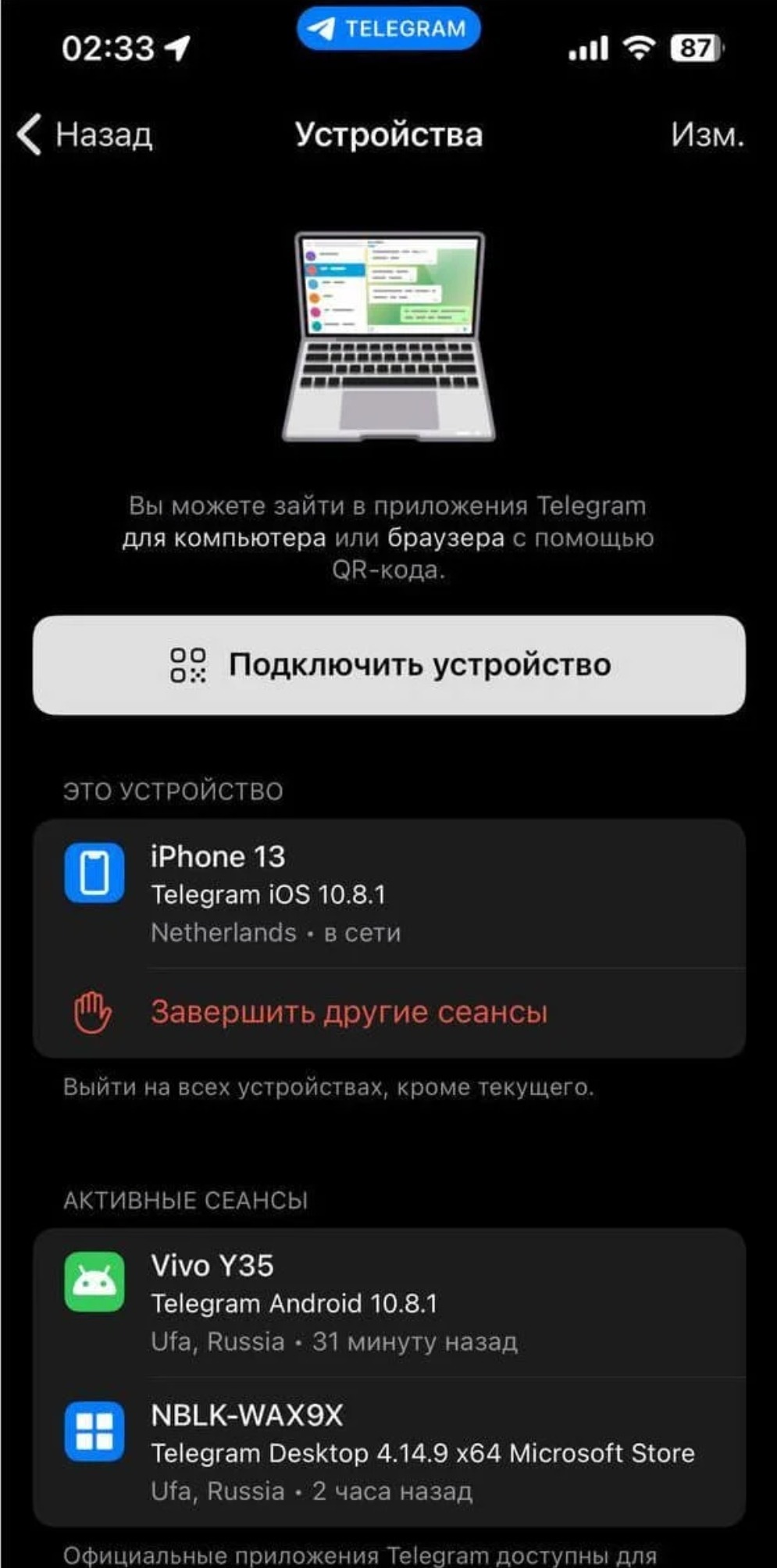
**Option 1 (General):** * **Unauthorized Access Detection: How to Know if Your System Was Breached** **Option 2 (More Specific):** * **Detecting Unauthorized Logins: Has Your Account Been Hacked?** **Option 3 (Question Format):** * **Was Your Account Compromised? Detecting Unauthorized Access Attempts**
How to Tell if There Have Been Unauthorized Logins? Every day, internet users face the risk of unauthorized logins to…
Read More
How to Protect Server Files from Unauthorized Changes
How to Protect Server Files from Changes? There are several ways to ensure the security of server files from changes.…
Read More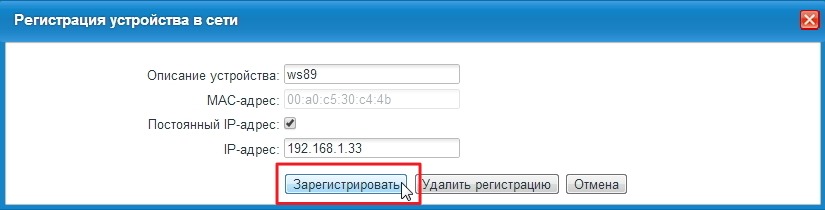
How to Enable MAC Address Filtering (and Secure Your Network)
How to Enable MAC Address Filtering? MAC address filtering is an effective method for securing your network. A MAC address…
Read More
How to Protect Your Server from DNS Spoofing Attacks
How to Protect Your Server from DNS Spoofing DNS spoofing is a common type of attack on servers. In this…
Read More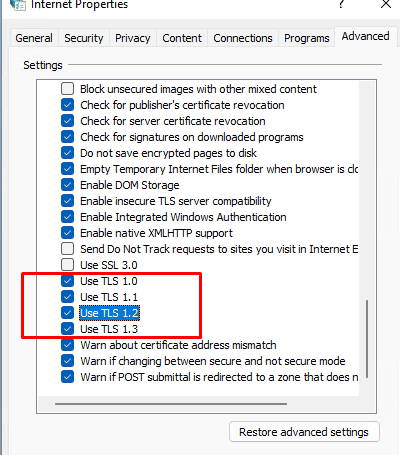
Disable Old TLS Versions on Your Server: A Security Guide
How to Disable Old TLS Versions on a Server? In our time, the security of networks and servers plays a…
Read More
How to Set Up a VPN for Secure Access: A Step-by-Step Guide
How to Set Up a VPN for Secure Access? Internet security has become one of the key issues of our…
Read More
Protect Your Server: A Guide to Preventing Phishing Attacks
How to Protect Your Server from Phishing Attacks? Phishing attacks are one of the most common threats in information security.…
Read More
Securing Redis: Protecting Your Data from Unauthorized Access
How to Protect Redis from Unauthorized Access? Redis is a high-performance database management system widely used for data caching, session…
Read MoreSearch
Recent Posts
- How to Test Your VDS Windows Hard Drive Speed? 18.11.2025
- How to Install and Configure Fail2ban on Ubuntu VPS: A Step-by-Step Guide 18.11.2025
- How to Configure Nagios Alerts on a Dedicated Server: A Step-by-Step Guide 17.11.2025
- How to View Running Processes on a Linux Ubuntu VPS in 2025 17.11.2025
- Simple Script to Monitor VDS Disk Space (and Avoid Running Out!) 16.11.2025
Categories
- Backups & Data Recovery [EN] (64)
- Backups & Recovery [EN] (1)
- Backups and Data Recovery [EN] (65)
- Backups and Recovery [EN] (2)
- Data Backup & Recovery [EN] (18)
- Data Backup and Recovery [EN] (19)
- Guides and Tutorials [EN] (1)
- Internet Security [EN] (12)
- Performance & Optimization [EN] (30)
- Server Monitoring & Management [EN] (91)
- Server Monitoring and Management [EN] (44)
- Server Security [EN] (129)
- Software & Tools [EN] (13)
- Tech Support & Troubleshooting [EN] (79)
- Technical Support [EN] (79)
- Technical Support & Troubleshooting [EN] (7)
- Troubleshooting [EN] (36)
- VPS & Virtualization [EN] (201)
- VPS and virtualization [EN] (1)
- VPS VDS RDP [EN] (12)
- VPS/VDS/RDP [EN] (93)
- Мониторинг и управление сервером [RU] [EN] (54)
- Техническая поддержка и устранение проблем [EN] (1)
