Server Security [EN]
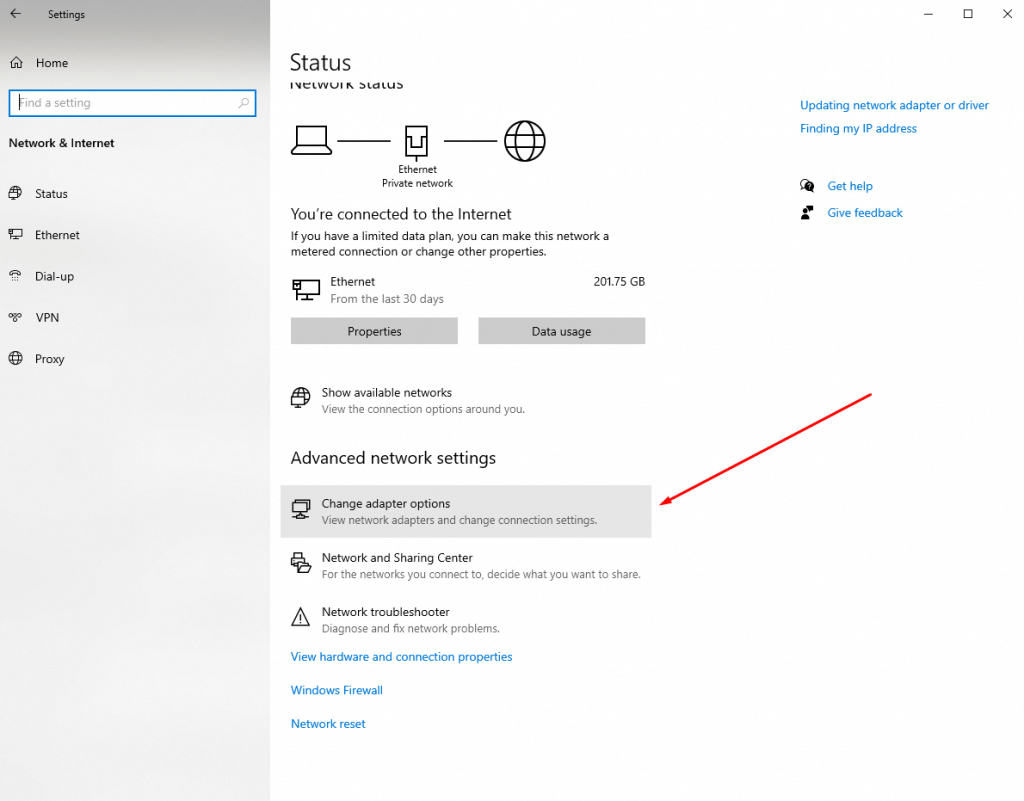
How to Disable IPv6 When It’s Not Being Used: A Simple Guide
How to Disable IPv6 If It’s Not Being Used? IPv6 is a newer version of the Internet Protocol intended to…
Read More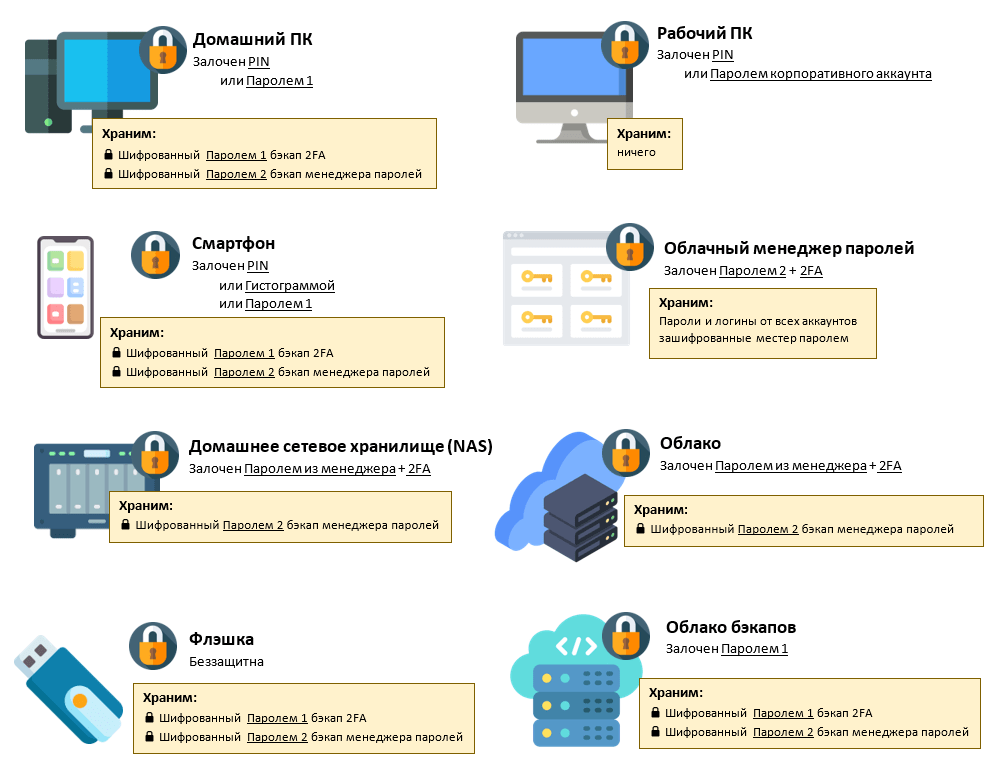
Secure Password Storage: Best Practices & Configuration Guide
How to Configure Secure Password Storage? Today, in the modern world, cybersecurity is becoming an increasingly relevant and integral part…
Read More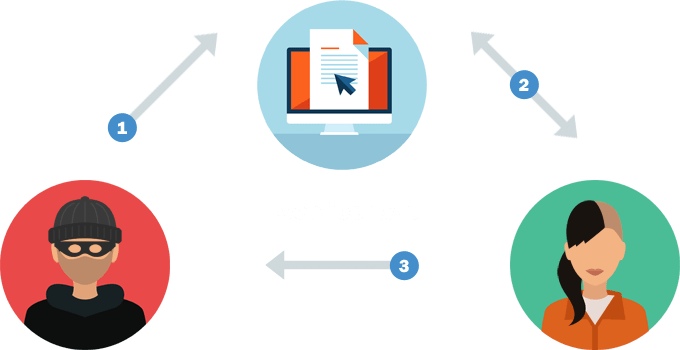
Protect Your Server: A Guide to Preventing Cross-Site Scripting (XSS) Attacks
«`html How to Protect Your Server from XSS Attacks? How to Protect Your Server from XSS Attacks? Cross-site scripting (XSS)…
Read More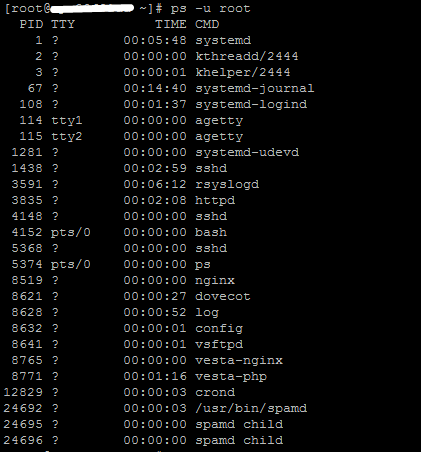
How to Check Running Processes on Your Server
How to Find Out Which Processes Are Running on the Server? If you’re a server administrator or just want to…
Read More
How to Remove Old SSH Keys: A Security Guide
How to Remove Old SSH Keys? SSH keys play an important role in the security of your server. However, over…
Read More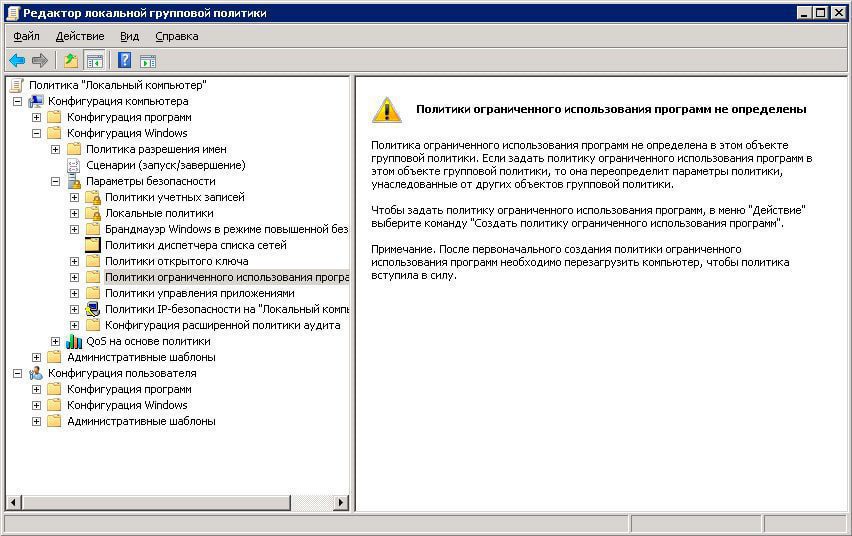
How to Block Software Installation on a Server: A Security Guide
How to Prevent New Software Installation on a Server? Installing new software on a server can pose a risk to…
Read More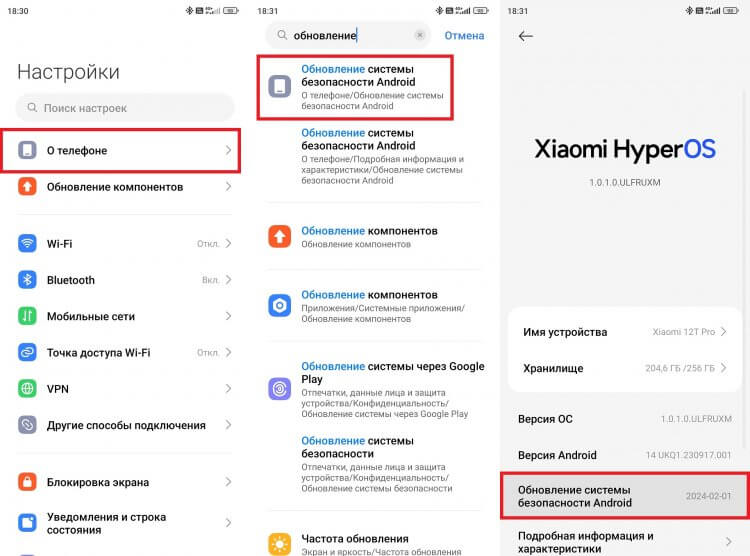
How to Check for Security Updates and Identify Vulnerable Packages
How to Find Out Which Packages Need Security Updates? In today’s world, internet security plays a crucial role. Many malicious…
Read More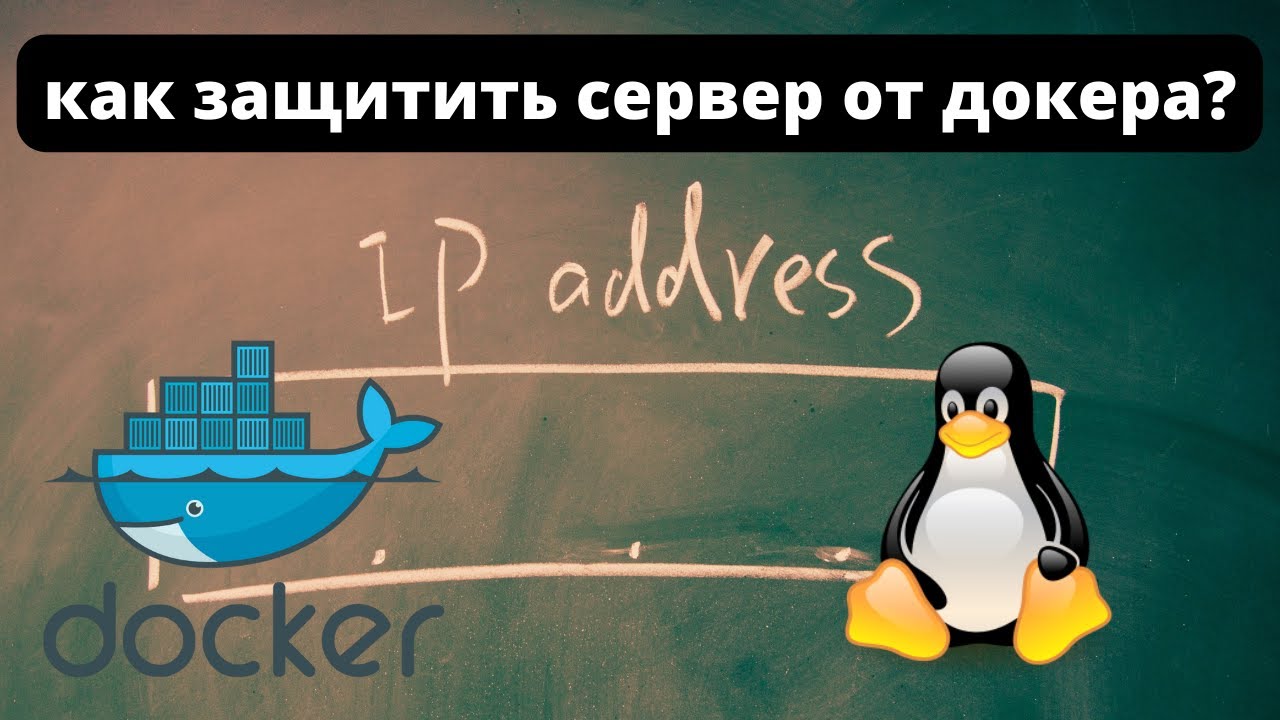
Securing Docker Containers on Your Server: A Comprehensive Guide
How to Secure Docker Containers on a Server? Docker containers are a convenient way to package applications and their dependencies…
Read More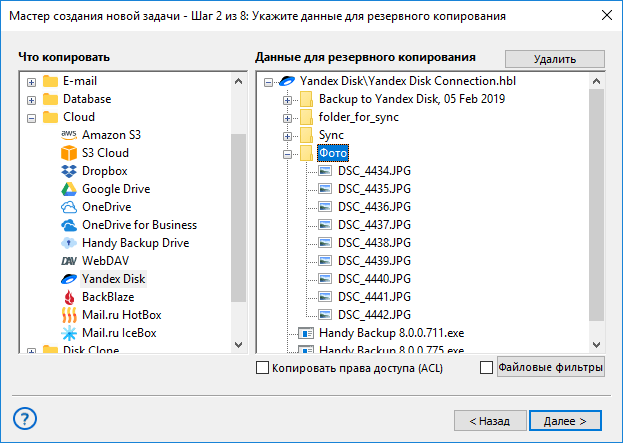
How to Verify Backup Integrity: A Comprehensive Guide
How to Check Backup Integrity? Backups are an integral part of any data protection system. However, it’s not enough to…
Read More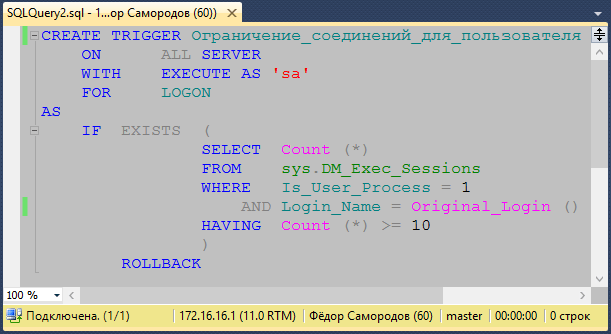
Limiting Server Connections: How to Prevent Overload
How to Limit the Number of Connections to a Server? For a server to function successfully, it’s crucial to be…
Read MoreSearch
Recent Posts
- How to Test Your VDS Windows Hard Drive Speed? 18.11.2025
- How to Install and Configure Fail2ban on Ubuntu VPS: A Step-by-Step Guide 18.11.2025
- How to Configure Nagios Alerts on a Dedicated Server: A Step-by-Step Guide 17.11.2025
- How to View Running Processes on a Linux Ubuntu VPS in 2025 17.11.2025
- Simple Script to Monitor VDS Disk Space (and Avoid Running Out!) 16.11.2025
Categories
- Backups & Data Recovery [EN] (64)
- Backups & Recovery [EN] (1)
- Backups and Data Recovery [EN] (65)
- Backups and Recovery [EN] (2)
- Data Backup & Recovery [EN] (18)
- Data Backup and Recovery [EN] (19)
- Guides and Tutorials [EN] (1)
- Internet Security [EN] (12)
- Performance & Optimization [EN] (30)
- Server Monitoring & Management [EN] (91)
- Server Monitoring and Management [EN] (44)
- Server Security [EN] (129)
- Software & Tools [EN] (13)
- Tech Support & Troubleshooting [EN] (79)
- Technical Support [EN] (79)
- Technical Support & Troubleshooting [EN] (7)
- Troubleshooting [EN] (36)
- VPS & Virtualization [EN] (201)
- VPS and virtualization [EN] (1)
- VPS VDS RDP [EN] (12)
- VPS/VDS/RDP [EN] (93)
- Мониторинг и управление сервером [RU] [EN] (54)
- Техническая поддержка и устранение проблем [EN] (1)
