Server Security [EN]
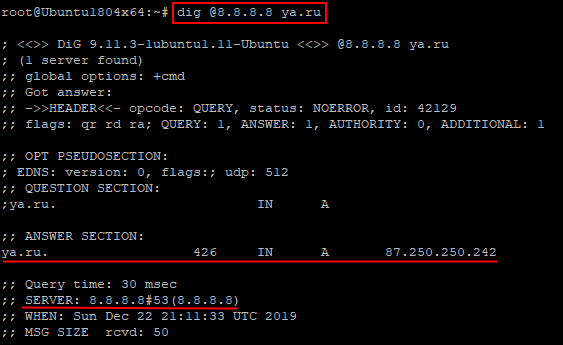
How to Check Allowed Connections to Your Server
How to Check Allowed Connections to the Server? Understanding which connections to the server are allowed is an important aspect…
Read More
Securing Your Server: Protecting Against Attacks via Exposed Databases
How to Protect Your Server from Attacks via Open Databases? Attacks on servers through open databases are becoming increasingly common…
Read More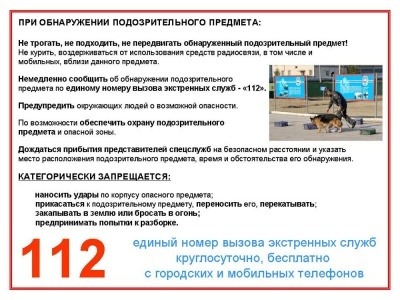
Automated Alerts for Suspicious Activity: A How-To Guide
How to Automatically Get Notified About Suspicious Events? In this day and age, information security plays a huge role. It’s…
Read More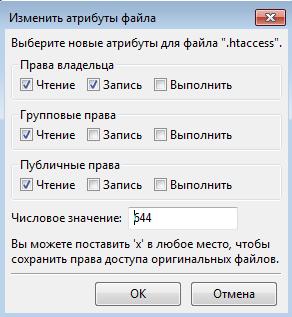
Best File Permissions for Your Server: A Security Guide
What File Permissions Should Be Set on the Server? File permissions on the server are a crucial aspect of your…
Read More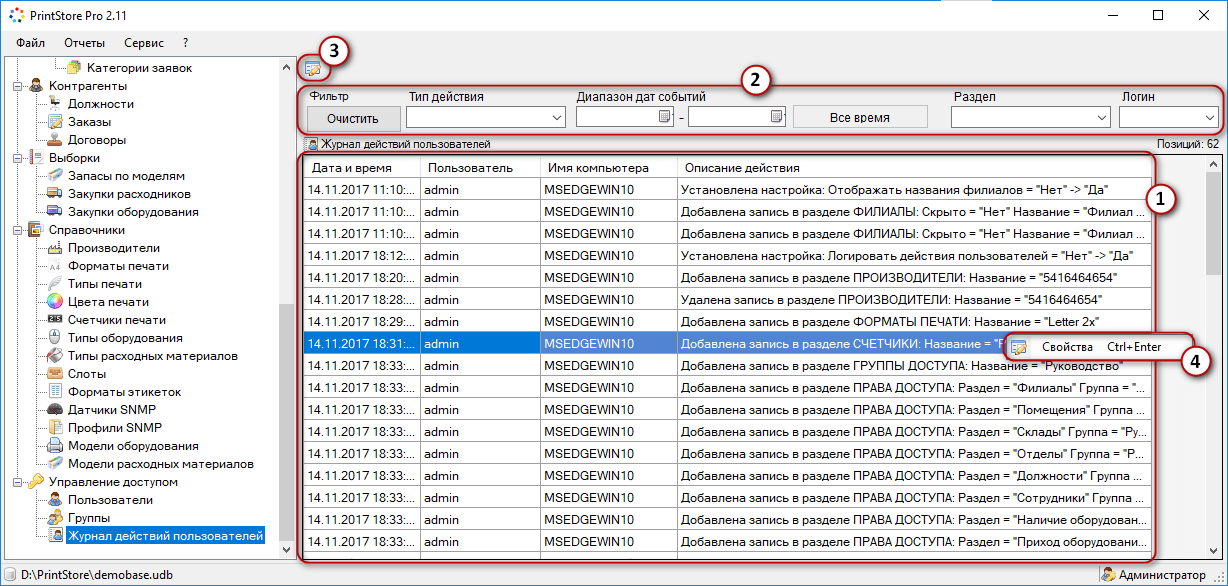
How to Set Up User Activity Logging: A Comprehensive Guide
How to Set Up User Activity Logging? User activity logging is an important part of any web application or website.…
Read More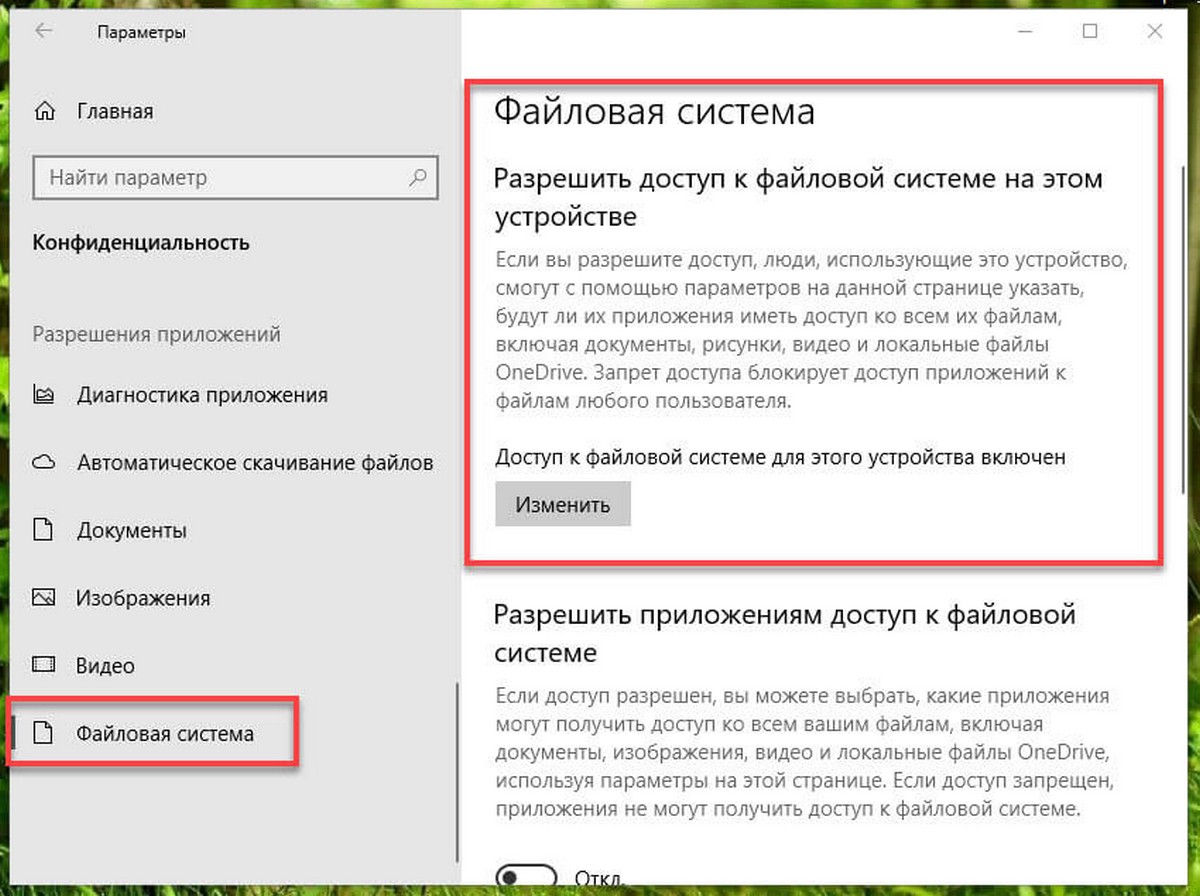
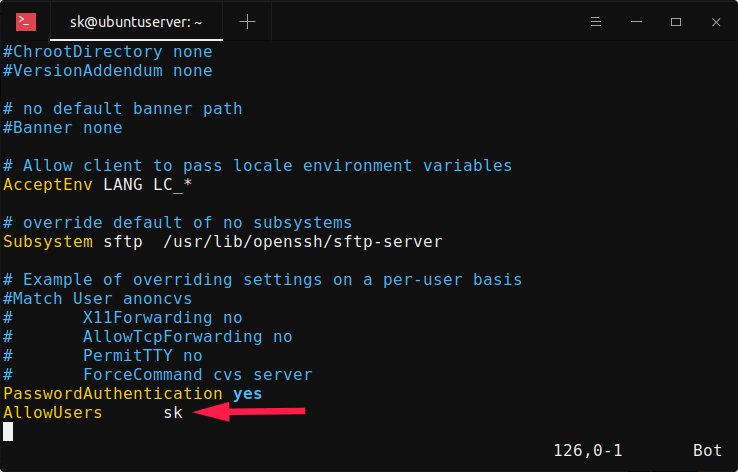
How to Restrict Access to Critical Files: A Security Guide
How to Restrict Access to Critical Files? In our time, cybersecurity is becoming an increasingly important topic. Attackers are constantly…
Read More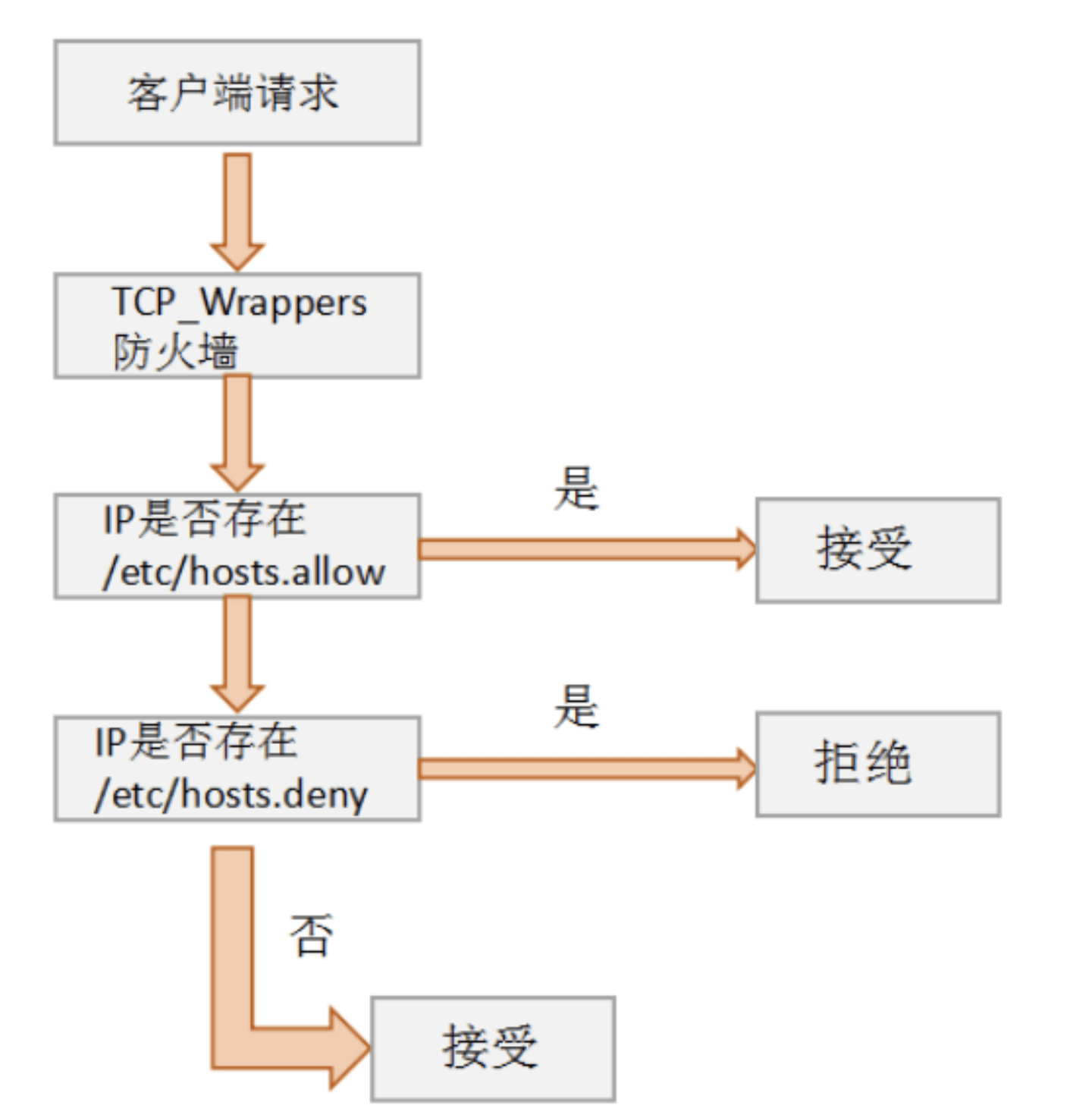
TCP Wrappers: Secure Your Server with Access Control
How to Use TCP Wrappers for Access Control? Protecting a server from unauthorized access is one of the most important…
Read More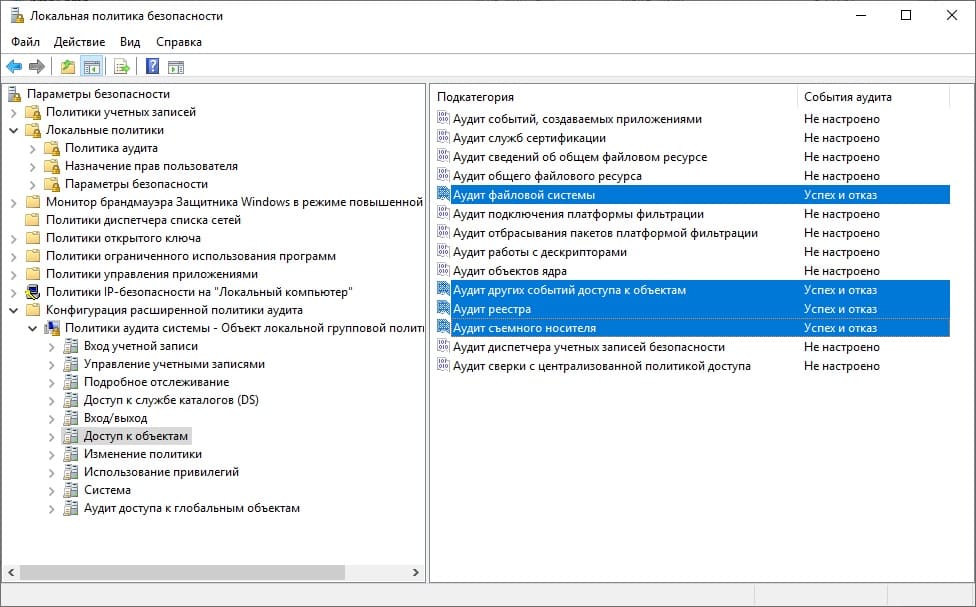
How to Enable Audit Logging for All Changes on Your Server
How to Enable Auditing of All Changes on a Server? Auditing changes on a server is an important function for…
Read More
How to Protect Your Server from Botnet Attacks: A Complete Guide
How to Protect Your Server from Botnet Attacks? Botnets are networks of infected computers controlled by attackers and can be…
Read MoreSearch
Recent Posts
- How to Test Your VDS Windows Hard Drive Speed? 18.11.2025
- How to Install and Configure Fail2ban on Ubuntu VPS: A Step-by-Step Guide 18.11.2025
- How to Configure Nagios Alerts on a Dedicated Server: A Step-by-Step Guide 17.11.2025
- How to View Running Processes on a Linux Ubuntu VPS in 2025 17.11.2025
- Simple Script to Monitor VDS Disk Space (and Avoid Running Out!) 16.11.2025
Categories
- Backups & Data Recovery [EN] (64)
- Backups & Recovery [EN] (1)
- Backups and Data Recovery [EN] (65)
- Backups and Recovery [EN] (2)
- Data Backup & Recovery [EN] (18)
- Data Backup and Recovery [EN] (19)
- Guides and Tutorials [EN] (1)
- Internet Security [EN] (12)
- Performance & Optimization [EN] (30)
- Server Monitoring & Management [EN] (91)
- Server Monitoring and Management [EN] (44)
- Server Security [EN] (129)
- Software & Tools [EN] (13)
- Tech Support & Troubleshooting [EN] (79)
- Technical Support [EN] (79)
- Technical Support & Troubleshooting [EN] (7)
- Troubleshooting [EN] (36)
- VPS & Virtualization [EN] (201)
- VPS and virtualization [EN] (1)
- VPS VDS RDP [EN] (12)
- VPS/VDS/RDP [EN] (93)
- Мониторинг и управление сервером [RU] [EN] (54)
- Техническая поддержка и устранение проблем [EN] (1)